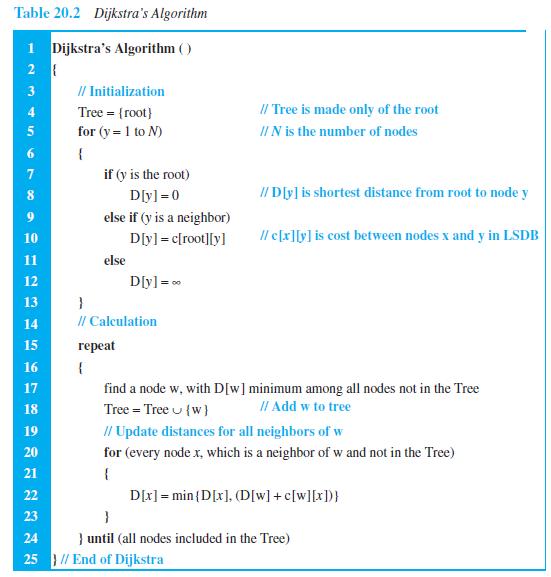
Write a program to simulate the link-state algorithm (Table 20.2). Dijkstra's Algorithm ( ) // Initialization Tree
Question:
Write a program to simulate the link-state algorithm (Table 20.2).
Transcribed Image Text:
Dijkstra's Algorithm ( ) // Initialization Tree = {root} 3 I/ Tree is made only of the root 4. for (y = 1 to N) II N is the number of nodes { if (y is the root) 8. Dly] =0 // D[y] is shortest distance from root to node y else if (y is a neighbor) D[yl = c[root][y] Il c[x][y] is cost between nodes x and y in LSDB 10 11 else D[y]= 0 12 13 } 14 // Calculation 15 герeat 16 { 17 find a node w, with D[w]minimum among all nodes not in the Tree 18 Tree = Tree u {w} II Add w to tree // Update distances for all neighbors of w 19 20 for (every node x, which is a neighbor of w and not in the Tree) 21 D[x] = min {D[x], (D[w] + c[w][x])} 22 23 24 } until (all nodes included in the Tree) 25 } // End of Dijkstra
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 90% (10 reviews)
The second program simulates the LinkState protocol ...View the full answer

Answered By

PALASH JHANWAR
I am a Chartered Accountant with AIR 45 in CA - IPCC. I am a Merit Holder ( B.Com ). The following is my educational details.
PLEASE ACCESS MY RESUME FROM THE FOLLOWING LINK: https://drive.google.com/file/d/1hYR1uch-ff6MRC_cDB07K6VqY9kQ3SFL/view?usp=sharing
3.80+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21). Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from application. Make a packet...
-
Write a program to simulate the sending-site FSMs for the Go-Back-N protocol (Figure 23.27).
-
Write a program to simulate the sending-site FSMs for the Selective Repeat protocol (Figure 23.34). Figure 23.34 FSMS for SR protocol Sender Time-out. Resend all outstanding packets in window. Reset...
-
Assume a portfolio of two assets, with $10m invested in asset 1 and $5m invested in asset 2. The per pound covariance matrix of the two assets is: Asset 1 Asset 2 The best hedge of asset 2 is: Asset...
-
Assume that you are going to start a small business of your own. Describe the business and discuss the following: What costs you would incur? What competition you might experience How you would...
-
What is a non-interest-bearing note? How does accounting for a short-term non-interest-bearing note differ from a short-term interest-bearing note?
-
On July 31, 2010, the Accounts Receivable balance of Questor Application, Inc., is $320,000. The Allowance for Uncollectible Accounts has a $6,400 credit balance. Questor prepares the following aging...
-
The following are system benefits for Interglobal Paper Company (from Problem 10): Year Benefits 1 ........... $55,000 2 ...........75,000 3 ...........80,000 4 ...........85,000 a. Use the costs of...
-
How do organizational change management theories, such as Lewin's Force Field Analysis or Kotter's Eight-Step Process, inform successful implementation strategies for large-scale organizational...
-
NOTE: include a copy of your equations and equations/code with your plots 1. (50 points) A non-afterburning turbojet is being designed for operation at an altitude of 15 km and a Mach number of 1.8....
-
Write a program to simulate the distance-vector algorithm (Table 20.1). for (y = 1 to N) { if (y is a neighbor) D[y] = c[myself][y] else 10 D[y] = 0 11 } send vector {D[1], D[2], ..., D[N]} to all...
-
Write a program to simulate the path-vector algorithm (Table 20.3). Table 20.3 Path-vector algorithm for a node 1 Path_Vector_Routing ( ) 2 { // Initialization for (y = 1 to N) 3 { if (y is myself)...
-
Shown here are condensed income statements for two different companies (assume no income taxes). Required 1. Compute times interest earned for Ellis Company and for Seidel Company. 2. What happens to...
-
What are the potential ecological and evolutionary consequences of genetic bottlenecks and reduced genetic diversity in small populations, particularly in the context of endangered species...
-
What are the various stages of a Linux process it passes through?
-
Canton Corporation is considering introducing a new product Model X with a recommended unit selling price of $65 with a target profit of $100,000. The product can be manufactured using either Option...
-
Showtime Company's ending inventory at December 31, 2023, includes the following items: Net Realizable Units on Product Hand Unit Cost BB 36 $ 111 FM 15 146 MB 50 187 SL 54 79 Value Per Unit $ 116...
-
Submit a Reflection Report about the Negotiation Scenario - Taking the perspective of the Truckers/Protesters. Negotiation scenario In 2022 a group of people organized a protest against the ongoing...
-
Repeat the analysis for Tim Hortons (www.timhortons.com). In addition to the EDGAR site, check www.sedar.com for Canadian filings.
-
Find the inverse, if it exists, for the matrix. -1
-
Explain why the MAC protocol is more important in wireless LANs than in wired LANs.
-
A program to simulate the calculation of traditional checksum.
-
In an 802.11, give the value of the address 2 field in each of the following situations (left bit defines To DS and right bit defines From DS). a. 00 b. 01 c. 10 d. 11
-
. What is one direct way in which children impact their own acculturation? How does the example you chose show the child's impact? . What is one indirect way in which children impact their own...
-
Suppose demand for domestic airline tickets is given by P = 800 - 3Q and supply is given by P = 10 + 2Q. The government, in an attempt to encourage Australians to consider driving instead of flying,...
-
You've been an entry-level financial analyst for six months. Your supervisor plans to fill another entry-level financial analyst position on your team. Your supervisor has asked you come up with a...

Study smarter with the SolutionInn App


