Question: Consider sender 2 in Figure 7.6. What is the sender's output to the channel (before it is added to the signal from sender 1). Z
Consider sender 2 in Figure 7.6. What is the sender's output to the channel (before it is added to the signal from sender 1). Z2i,m?
Figure 7.6
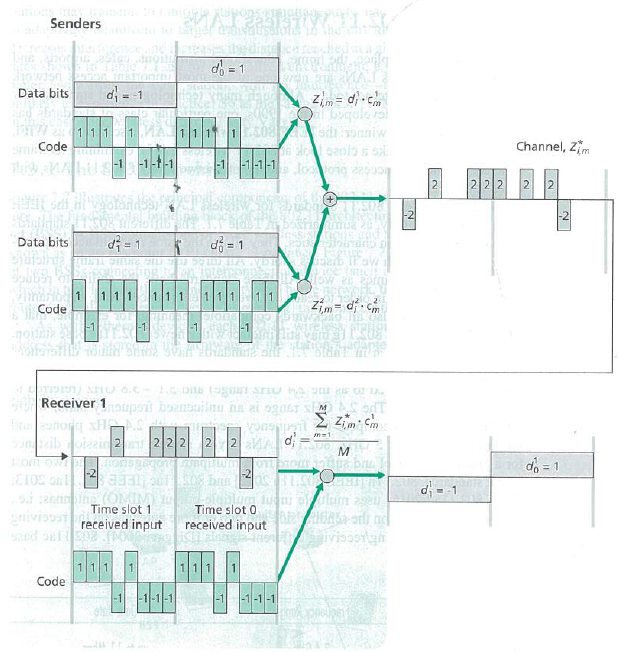
Senders T 3510g no 150 299R INRITOnini d=-1 Data bits Demic Code Data bits d=1 Bilibid men SHINE SU powoppling Bobb 1 1 1 1 htlg-1-1-1-1 461 Code 17 STID TILIN SHREY grivissut sand 581 Code 111 1 1 1 5 for THELE BE -1 Rom QW 50 ETOS onl 83811 si cantinthe (OMIN Time slot 1 received input -2 sponta Zim= d)-cm al bogole val 11 1 12.508 Todi sonniw lo saol5 s sol fooo70 285900 111 DTP) ATTU 6.6- 1.G. Dis togost sro A kis of the Receiver 1nnupsit boensoilmu na ai ogast T Brunong xH AS Vousipent 53muzib olzein 2 2 2 2 2 2 14 d |-| do = 1 -1 -1-1-1 d=1 COFDS 1 1 1 1 1 91005100 51 AD SER CASTLE TITUS Aiguis cact dloumino steblum Time slot 0 received input T -1-1-1 55215 aw gice much Now en epiru APCYNICY Zim= d.cm 2 M ABQHUMOTIONE The bru -2 OS BESTOFEFFI ai ollum ageu ARRIBA-arl Divisostigh Zimm M=1 N d=1 222 Channel, Zim 2 2 N do = 1
Step by Step Solution
3.38 Rating (170 Votes )
There are 3 Steps involved in it
Calculation of Sender 2 Output Sender 2 in Figure 76 is sending a data stream with ... View full answer

Get step-by-step solutions from verified subject matter experts


