Question: In Section 8.6. 1, it is shown that without sequence numbers, Trudy (a woman- in-the middle) can wreak havoc in an SSL session by interchanging
In Section 8.6. 1, it is shown that without sequence numbers, Trudy (a woman- in-the middle) can wreak havoc in an SSL session by interchanging TCP segments. Can Trudy do something similar by deleting a TCP segment? What does she need to do to succeed at the deletion attack? What effect will it have?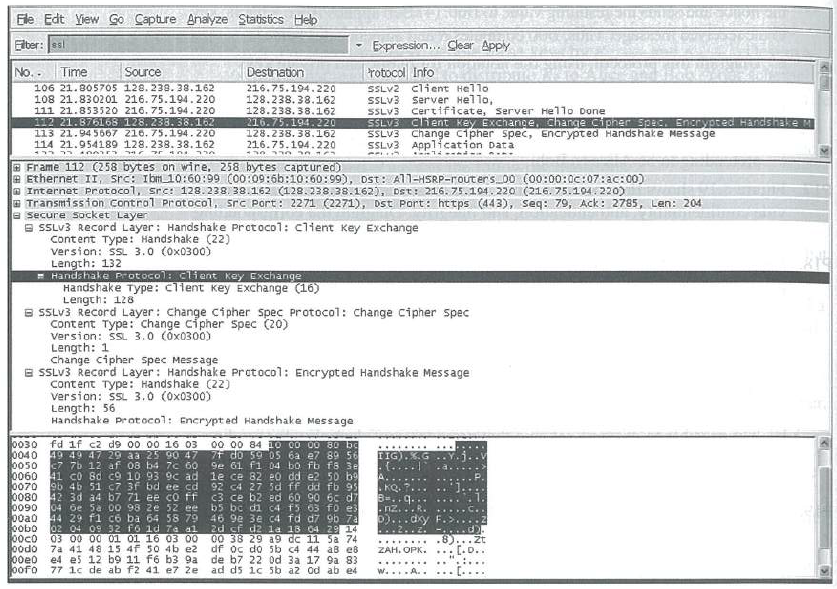 (Wire shark screenshot reprinted by permission of the Wire shark Foundation.)
(Wire shark screenshot reprinted by permission of the Wire shark Foundation.)
Ele Edt Yiew Go Capture Anayze Statistics Heb Elber: ss Expression.. Clear Apply rotocol Info No.. Time Source Destnation SSLV2 Client Hello SSLV3 SSLV3 SSLV3 Chent Key Exchange, Change Cipner Spec. Encrypted Handshake M SSLV3 Change cipher spec, Encrypted Handshake Message SSLV3 Application Data 106 21.805705 128. 238. 38.162 108 21.8302 01 216. 75.194.220 216.75.194.220 128.238. 38.162 128.238. 38.162 216.75.194.220 128.238. 38.162 216.75.194.220 Server Hel1o, Certificate, Server He1lo Done 111 21.853520 216. 75.194.220 112 21.876168 128. 238. 38.162 113 21.94 5667 216. 75.194.220 114 21.954189 128.238. 38.162 E Frame 112 (258 bytes on wire, 258 bytes captured) e Ethernet II, src: Ib10:60:99 (00:09:6b:10:60:99), Dst: All-HSRP-routers 00 C00:00:0c:07:ac:00) a Internet protocol, src: 128.238. 38.162 (128.238.38.162), Dst: 216. 75.104. 220 (216. 75.104.220) a Transmission Control Protocol, src Port: 2271 (2271), Dst Port: https (443), Seq: 79, Ack: 2785, Len: 204 a secure Socket Layen E SSLV3 Record Layer: Hands hake Protoco1: client Key Exchange content Type: Handshake (22) version: SL 3.0 (0x0300) Length: 132 Handshake Protocol: client Key Exchange Handshake Type: client Key Exchange (16) Length: 128 B SSLV3 Record Layer: Change Cipher spec Protocol: Change Cipher spec content Type: change cipher Spec (20) Version: SSL 3.0 (x0300) Length: 1 Change cipher spec Message E SSLV3 Record Layer: Handshake Protocol: Encrypt ed Handshake Message content Type: Handshake (22) version: SL 3.0 (0x0300) Length: 56 Handshake protocol: Encrypt ed Handshake Message 0030 0040 0050 0060 0070 0080 42 3d a4 b7 71 ee co ff 0090 00a0 oobo 00c0 0odo fd if c2 d9 00 00 16 03 49 49 47 29 aa 25 90 47 c7 7b 12 af 08 b4 7c 60 41 c0 8d c9 10 93 9c ad le ce 82 e0 dd e2 50 b 9b 46 51 c7 3f bd ee cd 00 00 84 10 00 00 80 ba 7f do 59 0S 6a e7 89 56 9e 61 fi 04 bo fb fs 3e TIG).K. {.... A... KQ. 7... 92 C4 27 5d ff dd fb 95 c3 ce b2 ed 60 90 6c d7 3=..g... b5 bc di c4 f5 03 fo e 46 9e 3e c4 fd d7 9b 7a 2d sf d2 1a 18 04 29 14 00 38 29 a9 dc 11 Sa 74 df oc do 5b c4 44 aB e8 de b7 22 0d 3a 17 9a 83 ad ds ic 5b a2 od ab e4 04 oe 5a 00 98 ze 52 ee 44 29 f1 c ba 64 58 79 02 04 09 32 fo ld 7a al 03 00 00 01 01 16 03 00 7a 41 48 15 4f 50 4b e2 e4 es 12 b9 11 f6 b3 9a 77 1c de ab f2 41 e7 e -nz...R b)...dky ...... ZAH. OPK. ... [.D.. w.A.. ::
Step by Step Solution
3.23 Rating (155 Votes )
There are 3 Steps involved in it
Again we suppose that SSL does not provide sequence numbers Suppose that Trudy ... View full answer

Get step-by-step solutions from verified subject matter experts


