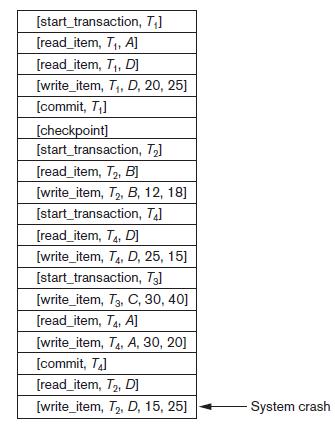
Figure 22.6 shows the log corresponding to a particular schedule at the point of a system crash
Question:
Figure 22.6 shows the log corresponding to a particular schedule at the point of a system crash for four transactions T1, T2, T3, and T4. Suppose that we use the immediate update protocol with checkpointing. Describe the recovery process from the system crash. Specify which transactions are rolled back, which operations in the log are redone and which (if any) are undone, and whether any cascading rollback takes place.
Figure 22.6
Transcribed Image Text:
[start_transaction, T;] [read_item, T,, A] [read_item, T,, D] [write_item, T,, D, 20, 25] [commit, T,] [checkpoint] [start_transaction, T3] [read_item, T2, B] [write_item, T2, B, 12, 18] [start_transaction, Ta] [read_item, T4, D] [write_item, T4, D, 25, 15] [start_transaction, T3] [write_item, T3, C, 30, 40] [read_item, T4, Al] [write_item, T4, A, 30, 20] [commit, T4) [read_item, T2, D] [write_item, T2, D, 15, 25] System crash
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (12 reviews)
In this example Transactions T1 T4 are committed transactions Transactions T2 T3 are uncommitted ...View the full answer

Answered By

Marvine Ekina
Marvine Ekina
Dedicated and experienced Academic Tutor with a proven track record for helping students to improve their academic performance. Adept at evaluating students and creating learning plans based on their strengths and weaknesses. Bringing forth a devotion to education and helping others to achieve their academic and life goals.
PERSONAL INFORMATION
Address: , ,
Nationality:
Driving License:
Hobbies: reading
SKILLS
????? Problem Solving Skills
????? Predictive Modeling
????? Customer Service Skills
????? Creative Problem Solving Skills
????? Strong Analytical Skills
????? Project Management Skills
????? Multitasking Skills
????? Leadership Skills
????? Curriculum Development
????? Excellent Communication Skills
????? SAT Prep
????? Knowledge of Educational Philosophies
????? Informal and Formal Assessments
0.00
0 Reviews
10+ Question Solved
Related Book For 

Fundamentals Of Database Systems
ISBN: 9780133970777
7th Edition
Authors: Ramez Elmasri, Shamkant Navathe
Question Posted:
Students also viewed these Computer science questions
-
Figure 23.6 shows the log corresponding to a particular schedule at the point of a system crash for the four transactions T1, T2, T3, and T4 of Figure 19.4. Suppose that we use the immediate update...
-
Suppose that we use the axial-flow pump of Fig. 11.13 to drive the leaf blower of Prob. 11.64. What approximate (a) Diameter and (b) Rotation speed are appropriate? (c) Is this a good design?
-
Suppose that we use a standardized variable x` = (x x)/sx, where sx is the standard deviation of x, in constructing a polynomial regression model. Using the data in Exercise 12-46 and the...
-
On January 1, 2020, Dole, Inc., declared a 15% stock dividend on its common stock when the market value of the common stock was $20 per share. The date of record is January 30, 2020, and the...
-
Define emotions and list the major emotional dimensions?
-
Consider the success factors listed in Table 7.5 is it worth undertaking SISP without top management involvement? Table 7.5 Success factors in SISP Rank Success factor order Respondents Primary Sum...
-
In 2002, the FASB concluded that the amortization of goodwill should no longer be required, and instead that goodwill be subject to an annual impairment test to verify that its value had not...
-
Holt Company paid out cash dividends at the end of each year as follows: Year Dividends 2014.....$250,000 2015.....$325,000 2016.....$400,000 Required: a. Assume that Holt had 250,000 common shares...
-
Consider two devices. Device " A " costs $ 1 , 0 0 0 , lasts 2 years, costs and gives you a cash flow of $ 1 0 0 / mo . Device " B " also costs $ 1 , 0 0 0 , lasts 3 years and gives a cash flow of $...
-
Determine Vo and ID for the networks for Fig. 2.155. 15 V ID Si +20 V Vo Si Si 0 Si Vo 4.7 k 2.2 k -5 V
-
Discuss the two-phase commit protocol used for transaction management in a DDBMS. List its limitations and explain how they are overcome using the three-phase commit protocol.
-
Suppose that we use the deferred update protocol for the example in Figure 22.6. Show how the log would be different in the case of deferred update by removing the unnecessary log entries; then...
-
Which would be more difficult to forecast 10 years from now: the number of 60 year-old residents or their average disposable income? Why?
-
The following are several figures reported for Allister and Barone as of December 31, 2021: Inventory Sales Investment income Cost of goods sold Operating expenses Allister Barone $ 490,000 $290,000...
-
In which situations, if any, would it be appropriate to use GPS when employees are 'off the clock"? The case discusses various GPS devices, but some companies in the U.S. and Europe have started...
-
Donald Transport assembles prestige manufactured homes. Its job-costing system has two direct-cost categories (direct materials and direct manufacturing labor) and one indirect-cost pool...
-
Will AI threaten jobs in Accounting or Finance? Which functions will be the safest from being replaced by AI? Which functions are the most threatened? As an employee, how do you stay safe in the fast...
-
b. The interest payment on June 30, Year 2, and the amortization of the bond premium, using the straight-line method. Round to the nearest dollar. 3. Determine the total interest expense for Year 1....
-
Take a look at Wendy's (www.wendys.com). How is this company attempting to set itself apart from its primary competitors of McDonald's (www.mcdonalds.com) and Burger King (www.burgerking.com)? What...
-
Determine the center and radius of each circle. Sketch each circle. 4x 2 + 4y 2 9 = 16y
-
The following true/false questions pertain to Figure 8.28. a. When a host in 172.16.1/24 sends a data-gram to an Amazon.con, server, the router Rl will encrypt the data-gram using IPsec. b. When a...
-
Suppose an SSL session employs a block cipher with CBC. True or false: The server sends to the client the IV in the clear.
-
Suppose Alice and Bob are communicating over an SSL session. Suppose an attacker, who does not have any of the shared keys. Inserts a bogus TCP segment into a packet stream with correct TCP checksum...
-
Quad Enterprises is considering a new 3 - year expansion project that requires an initial fixed asset investment of $ 2 . 8 million. The fixed asset falls into the 3 - year MACRS class ( MACRS Table...
-
payout of $1,215? % (Round to two decimal places.) Which is the best investment choice? (Select the best response.) O Investment one O Investment two O Investment three
-
the four key quantitative metrics used in the assessment of financial resilience and performance of investment projects by a firm

Study smarter with the SolutionInn App