Answered step by step
Verified Expert Solution
Question
1 Approved Answer
1. 2. Which of the followings are true about asymmetric cryptography? Check all that apply. Asymmetric cryptography is also called private-key cryptography. Key distribution and
1.
2.
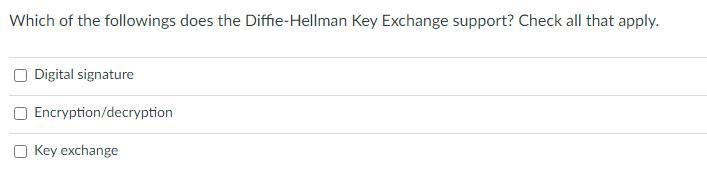
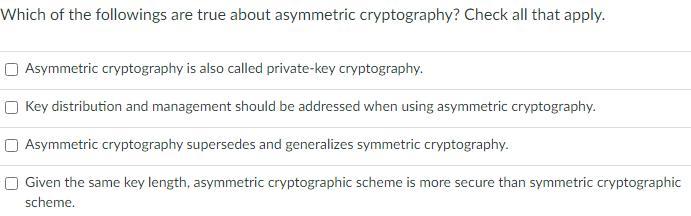
Which of the followings are true about asymmetric cryptography? Check all that apply. Asymmetric cryptography is also called private-key cryptography. Key distribution and management should be addressed when using asymmetric cryptography. Asymmetric cryptography supersedes and generalizes symmetric cryptography. Given the same key length, asymmetric cryptographic scheme is more secure than symmetric cryptographic scheme. Which of the followings does the Diffie-Hellman Key Exchange support? Check all that apply. Digital signature Encryption/decryption Key exchange
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


