Answered step by step
Verified Expert Solution
Question
1 Approved Answer
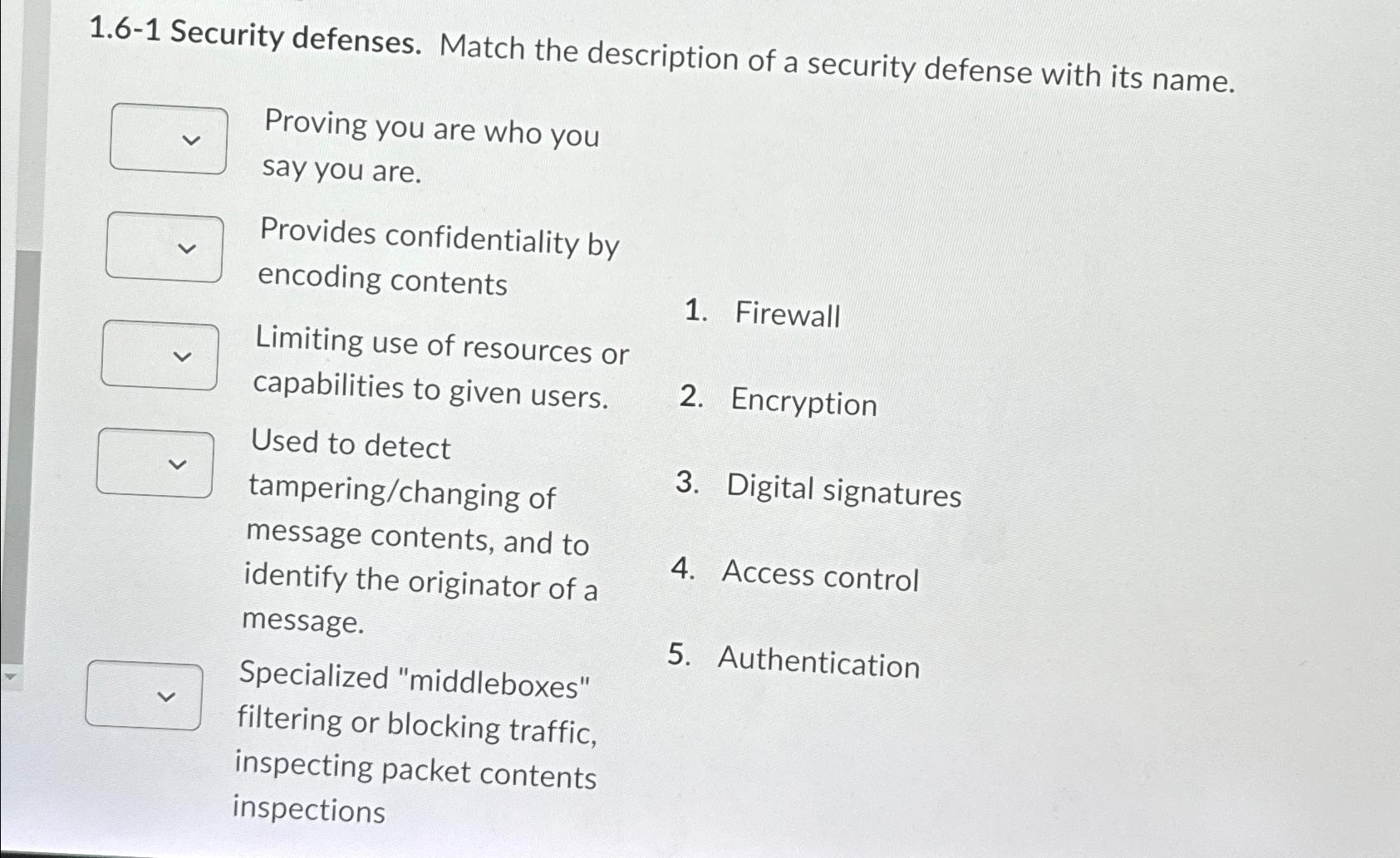
1 . 6 - 1 Security defenses. Match the description of a security defense with its name. Proving you are who you say you are.
Security defenses. Match the description of a security defense with its name.
Proving you are who you
say you are.
Provides confidentiality by encoding contents
Firewall
Limiting use of resources or capabilities to given users.
Encryption
Used to detect tamperingchanging of
Digital signatures
message contents, and to identify the originator of a
Access control message.
Specialized "middleboxes"
Authentication
filtering or blocking traffic, inspecting packet contents inspections
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started