Answered step by step
Verified Expert Solution
Question
1 Approved Answer
1. Bluebugging 2. Bluesnarfing 3. Eavesdropping 4. Evil twin S. Packet sniffing 6. Phreaking 7. Piggybacking 8. Vishing a. Intercepting Internet and other network transmissions
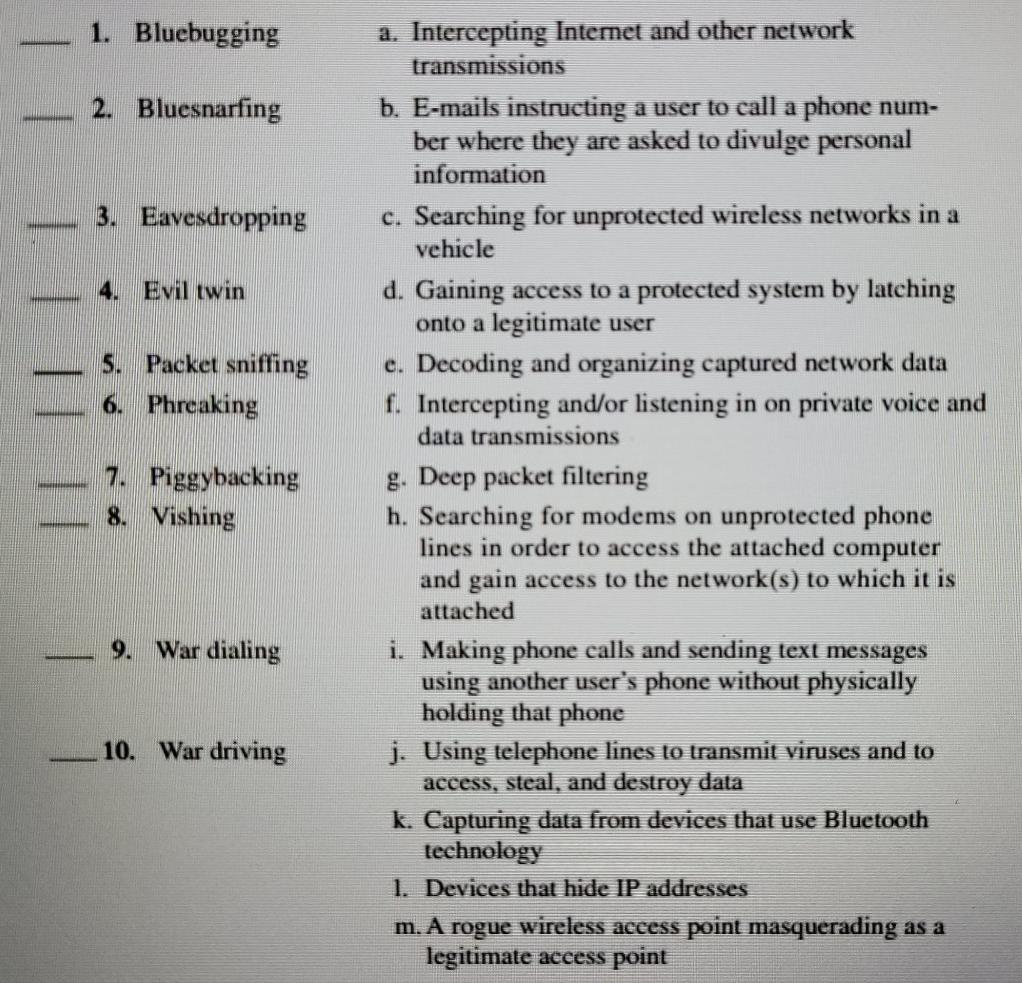
1. Bluebugging 2. Bluesnarfing 3. Eavesdropping 4. Evil twin S. Packet sniffing 6. Phreaking 7. Piggybacking 8. Vishing a. Intercepting Internet and other network transmissions b. E-mails instructing a user to call a phone num- ber where they are asked to divulge personal information c. Searching for unprotected wireless networks in a vehicle d. Gaining access to a protected system by latching onto a legitimate user e. Decoding and organizing captured network data f. Intercepting and/or listening in on private voice and data transmissions g. Deep packet filtering h. Searching for modems on unprotected phone lines in order to access the attached computer and gain access to the network(s) to which it is attached i. Making phone calls and sending text messages using another user's phone without physically holding that phone j. Using telephone lines to transmit viruses and to access, steal, and destroy data k. Capturing data from devices that use Bluetooth technology 1. Devices that hide IP addresses m. A rogue wireless access point masquerading as a legitimate access point 9. War dialing 10. War driving Computer Fraud and Abuse Techniques. Match the computer fraud and abuse technique in the left column with the scenario in the right column. The scenarios on the right may be used once, more than once, or not at all
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started