Answered step by step
Verified Expert Solution
Question
1 Approved Answer
1: in the figure below: B7-B3-A4-F7-DF-63 128.119.40.122 (1) 08-27-7C-7F-09-48 128.119.152.23 (2) B 21-44-8B-9C-C9-7F 128.119.152.173 D3-F3-DO-2C-53-17 128.119.25,207 D2-A2-AD-82-B8-9E 128.119.40.216 B8-96-00-BE-1C-C5 128.119.25.117 www. C 7C-D5-00-C8-26-86 128.119.25.205
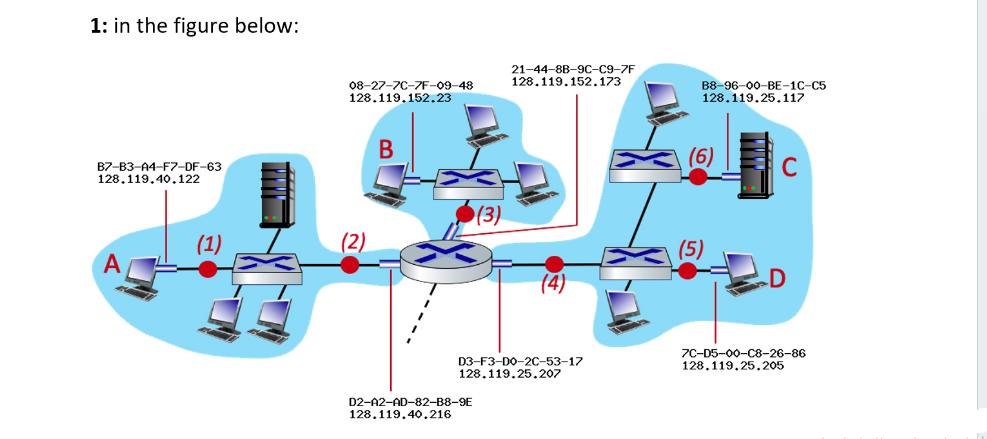
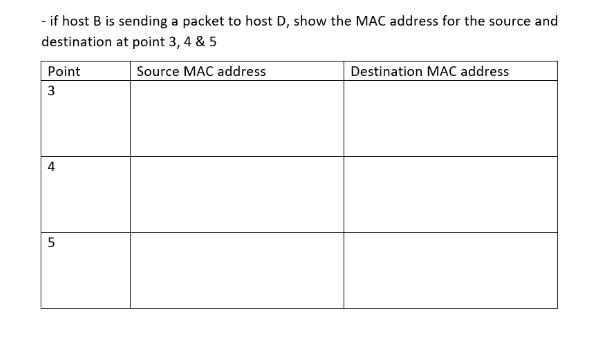
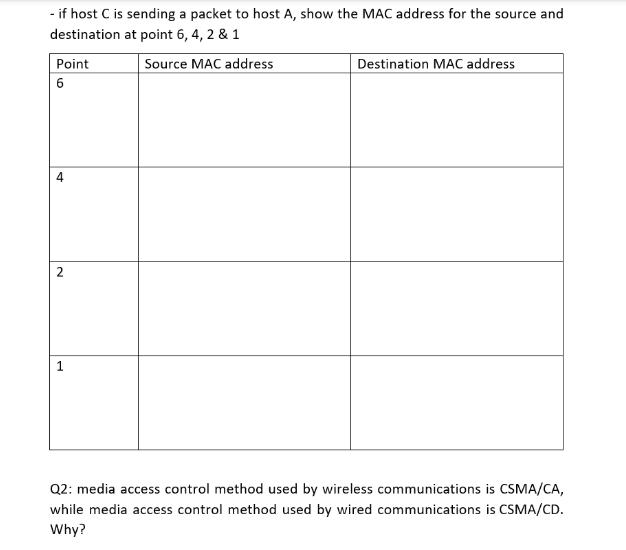
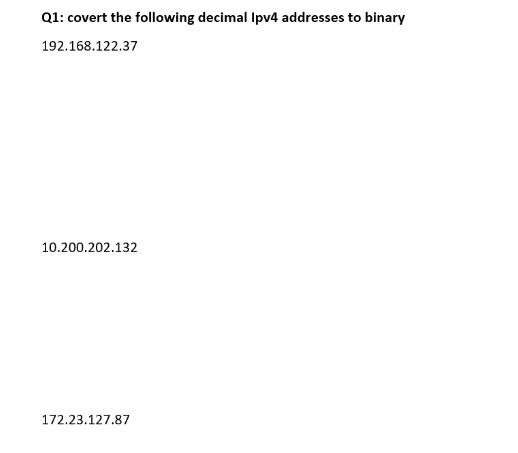
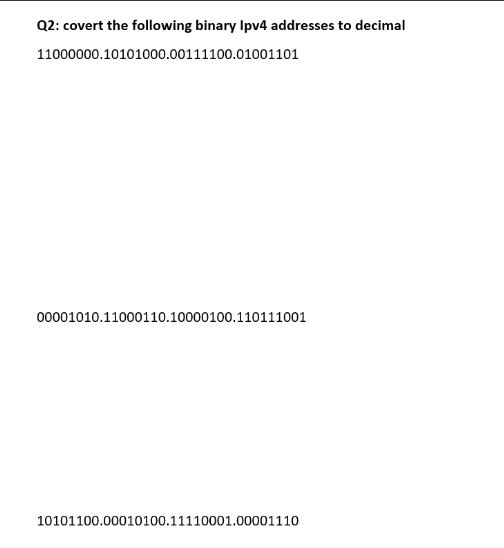
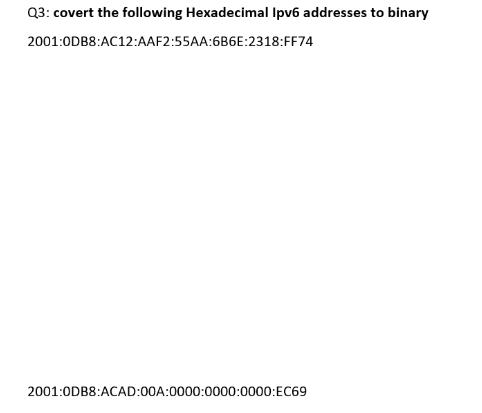
1: in the figure below: B7-B3-A4-F7-DF-63 128.119.40.122 (1) 08-27-7C-7F-09-48 128.119.152.23 (2) B 21-44-8B-9C-C9-7F 128.119.152.173 D3-F3-DO-2C-53-17 128.119.25,207 D2-A2-AD-82-B8-9E 128.119.40.216 B8-96-00-BE-1C-C5 128.119.25.117 www. C 7C-D5-00-C8-26-86 128.119.25.205 - if host B is sending a packet to host D, show the MAC address for the source and destination at point 3, 4 & 5 Point 3 4 5 Source MAC address Destination MAC address - if host C is sending a packet to host A, show the MAC address for the source and destination at point 6, 4, 2 & 1 Source MAC address Point 6 2 1 Destination MAC address Q2: media access control method used by wireless communications is CSMA/CA, while media access control method used by wired communications is CSMA/CD. Why? Q1: covert the following decimal Ipv4 addresses to binary 192.168.122.37 10.200.202.132 172.23.127.87 Q2: covert the following binary Ipv4 addresses to decimal 11000000.10101000.00111100.01001101 00001010.11000110.10000100.110111001 10101100.00010100.11110001.00001110 Q3: covert the following Hexadecimal Ipv6 addresses to binary 2001:0DB8:AC12:AAF2:55AA:6B6E:2318:FF74 2001:0DB8 ACAD:00A:0000:0000:0000:EC69
Step by Step Solution
★★★★★
3.47 Rating (160 Votes )
There are 3 Steps involved in it
Step: 1
The images you have provided pertain to computer networking and it appears there are multiple questions regarding MAC Media Access Control addresses and the conversion of IP addresses between decimal ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started