Question
1. Question. Consider the following C code fragment: 1 v o i d 2 f o o b a r ( ch a r a
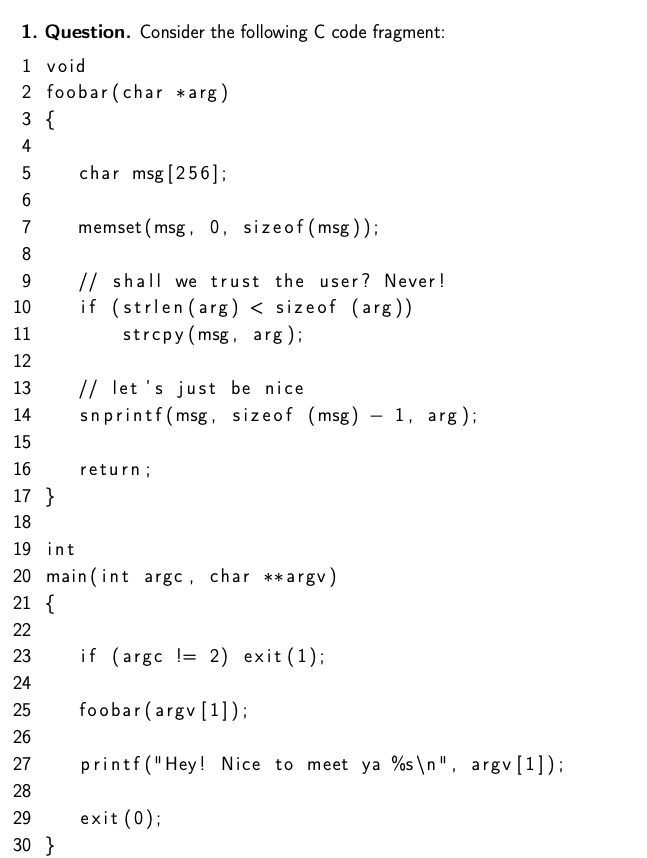
1. Question. Consider the following C code fragment: 1 v o i d 2 f o o b a r ( ch a r a rg ) 3 { 4 5 ch a r msg [ 2 5 6 ] ; 6 7 memset (msg , 0 , s i z e o f ( msg ) ) ; 8 9 // s h a l l we t r u s t th e u s e r ? Neve r ! 10 i f ( s t r l e n ( a rg )
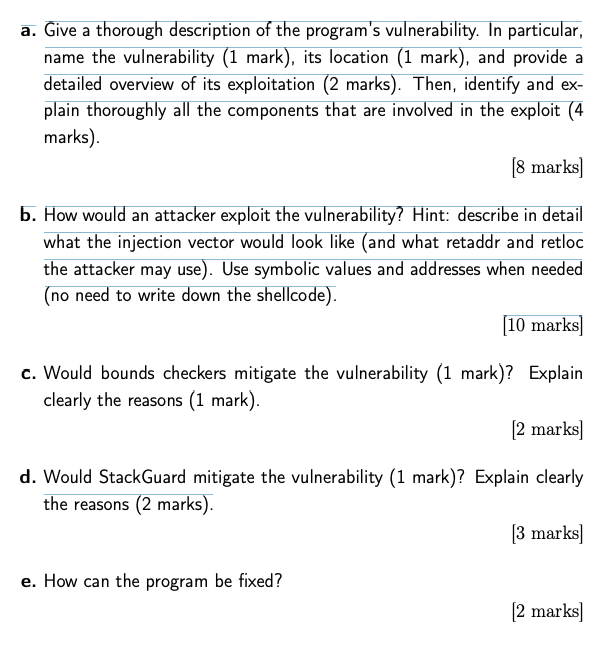
a. Give a thorough description of the programs vulnerability. In particular, name the vulnerability (1 mark), its location (1 mark), and provide a detailed overview of its exploitation (2 marks). Then, identify and explain thoroughly all the components that are involved in the exploit (4 marks). [8 marks]
b. How would an attacker exploit the vulnerability? Hint: describe in detail what the injection vector would look like (and what retaddr and retloc the attacker may use). Use symbolic values and addresses when needed (no need to write down the shellcode). [10 marks]
c. Would bounds checkers mitigate the vulnerability (1 mark)? Explain clearly the reasons (1 mark). [2 marks]
d. Would StackGuard mitigate the vulnerability (1 mark)? Explain clearly the reasons (2 marks).
a. Give a thorough description of the program's vulnerability. In particular, name the vulnerability (1 mark), its location (1 mark), and provide a detailed overview of its exploitation (2 marks). Then, identify and ex- plain thoroughly all the components that are involved in the exploit (4 marks) (8 marks b. How would an attacker exploit the vulnerability? Hint: describe in detail what the injection vector would look like (and what retaddr and retloc the attacker may use). Use symbolic values and addresses when needed (no need to write down the shellcode). [10 marks) c. Would bounds checkers mitigate the vulnerability (1 mark)? Explain clearly the reasons (1 mark). [2 marks d. Would StackGuard mitigate the vulnerability (1 mark)? Explain clearly the reasons (2 marks). [3 marks] e. How can the program be fixed? [2 marks] 10 ES 1. Question. Consider the following C code fragment: 1 void 2 foobar (char *arg) 3 { 4 5 char msg [256): 6 7 memset (msg, 0, sizeof(msg)); 8 9 // shall we trust the user? Never! if (strlen(arg)Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started