Question: 1. Who has the ultimate responsibility for information security within an organization? A. IT Security Officer B. Project Managers C. Department Directors D. Senior Management
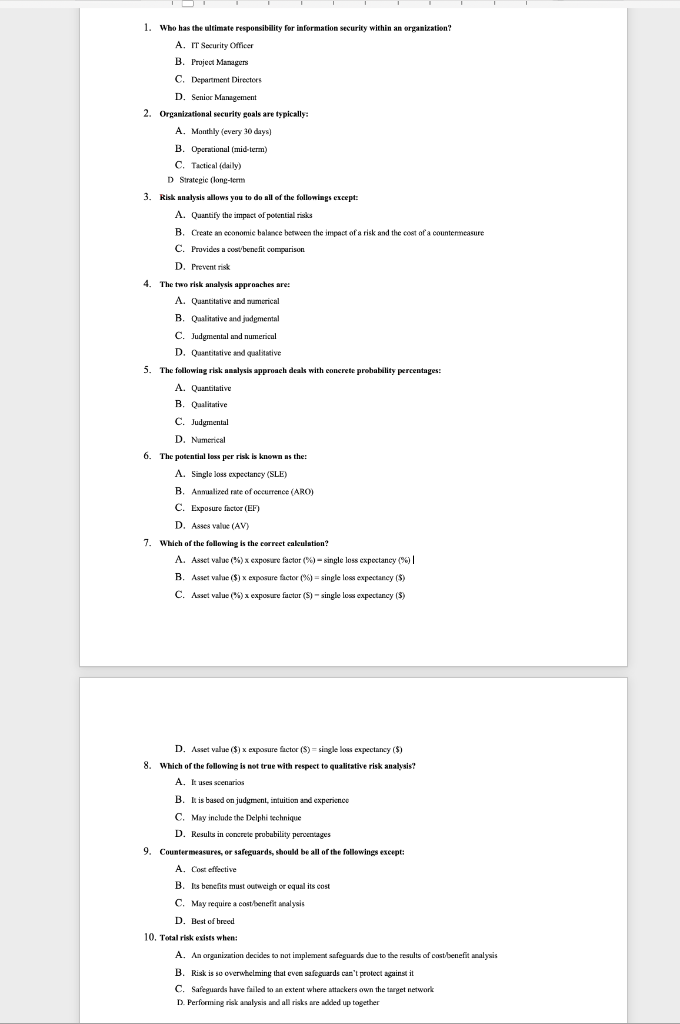
1. Who has the ultimate responsibility for information security within an organization? A. IT Security Officer B. Project Managers C. Department Directors D. Senior Management 2. Organizational security goals are typically: A. Monthly (every 30 days) B. Operational (mid-term) C. Tactical (daily) D Strategic long-term 3. Risk analysis allows you to do all of the followings except: A. Quantify the impact of potential risks B. Create an economie balsexe between the impact of a risk and the cost of a countermeasure C. Provides a cost benefit comparison D. Prevent risk 4. The two risk analysis approaches are: A. Quantitative and numerical B. Qualitative and judgmental C. Judgmental and numerical D. Quantitative and qualitative 5. The following risk analysis approach deals with concrete probability percentages: : A. Quantitative B. Qualitative C. Judgmental D. Numerical 6. The potential loss per risk is known as the A. Single loss expectancy (SLE) B. Analized rate of occurrence (ARO) C. Exposure factor (EF) D. Asses value (AV) 7. Which of the following is the correct calculation? A. Asset value (%) x exposure factor (%) - single loss expectancy (90)|| B. Asset vahe($) X exposure factor (%) = single loss expectancy ($) ) x ( C. Asset value%) x exposure factor ($) - single los expectancy (5) D. Asset valse ($) X exposure factor ($)=single lous expectaney ($) 8. Which of the following is not true with respect to qualitative risk analysis? A. It uses scenarios B. It is based on judgment, intuition and experience C. May include the Delphi technique D. Results in concrete prububility percentages 9. Countermeasures, or safeguards, should be all of the followings except: A. Cost effective B. Its bonsfits must outweigh or equal its cost C. May require a cost/benefit walysis D. Best of breed 10. Total risk exists when: A. An organization decides to not implement safeguards due to the results of cost benefit analysis B. Risk is so overwhelming that even safeguards can't protect against it C. Safeguards have failed to an extent where attackers own the target network D. Performing risk analysis and all risks are added up together
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


