Answered step by step
Verified Expert Solution
Question
1 Approved Answer
(10 points) Alice and Bob share the same pair of symmetric encryption algorithms, E and D. Also, they share the symmetric encryption key K. Suppose
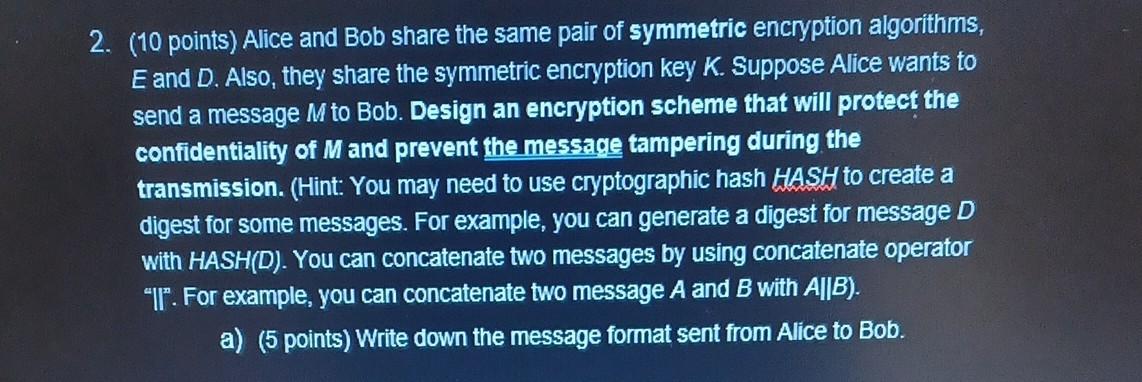
(10 points) Alice and Bob share the same pair of symmetric encryption algorithms, E and D. Also, they share the symmetric encryption key K. Suppose Alice wants to send a message M to Bob. Design an encryption scheme that will protect the confidentiality of M and prevent the message tampering during the transmission. (Hint: You may need to use cryptographic hash HASH to create a digest for some messages. For example, you can generate a digest for message D with HASH(D). You can concatenate two messages by using concatenate operator "II". For example, you can concatenate two message A and B with AB). a) (5 points) Write down the message format sent from Alice to Bob
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started