Question
A 6.0-m diameter cylindrical tank contains a hazardous material dissolved in mostly water. A leak occurred in the tank because a 0.1 m diameter
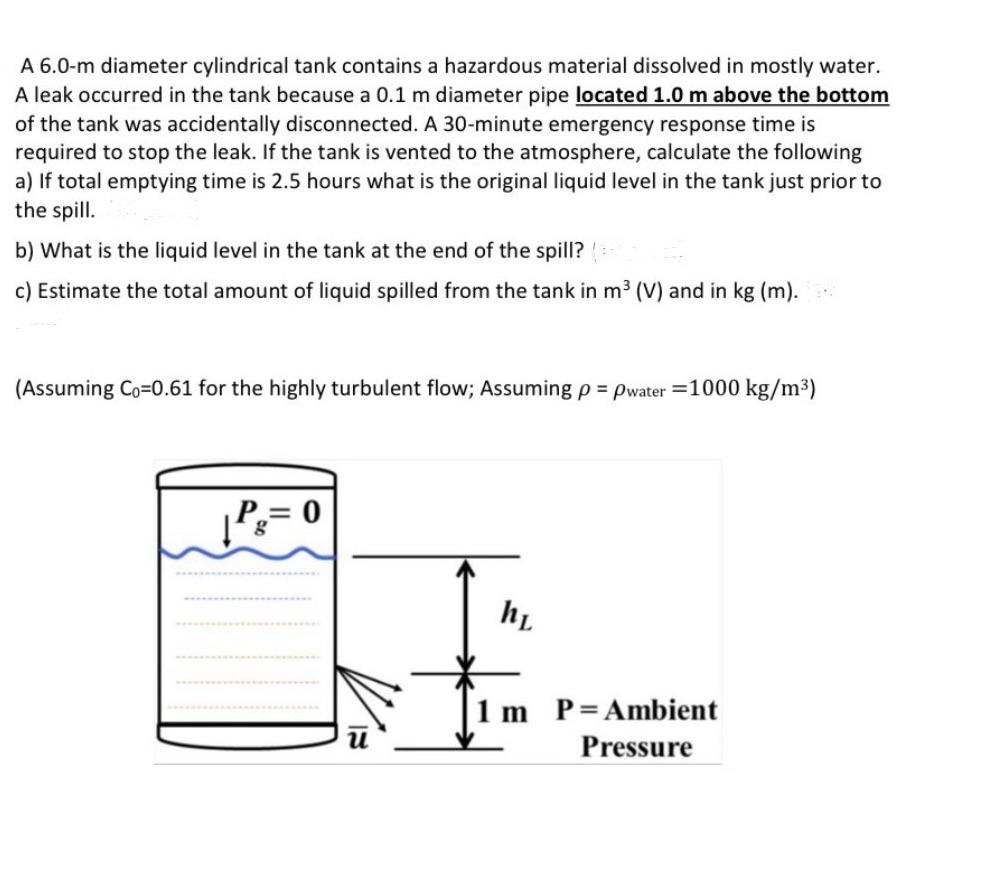
A 6.0-m diameter cylindrical tank contains a hazardous material dissolved in mostly water. A leak occurred in the tank because a 0.1 m diameter pipe located 1.0 m above the bottom of the tank was accidentally disconnected. A 30-minute emergency response time is required to stop the leak. If the tank is vented to the atmosphere, calculate the following a) If total emptying time is 2.5 hours what is the original liquid level in the tank just prior to the spill. b) What is the liquid level in the tank at the end of the spill? c) Estimate the total amount of liquid spilled from the tank in m (V) and in kg (m)... (Assuming Co=0.61 for the highly turbulent flow; Assuming p = pwater = 1000 kg/m) | P = 0 hL m P = Ambient Pressure
Step by Step Solution
3.30 Rating (141 Votes )
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Income Tax Fundamentals 2013
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
31st Edition
1111972516, 978-1285586618, 1285586611, 978-1285613109, 978-1111972516
Students also viewed these Chemical Engineering questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App



