Question
1.When shopping for a firewall, what 3 pieces of documentation should you bring to a meeting with a vendor or consultant on the purchase 2.
1.When shopping for a firewall, what 3 pieces of documentation should you bring to a meeting with a vendor or consultant on the purchase
2. Complete the following statement: Access control lists or rules are created for each ______________ on the firewall
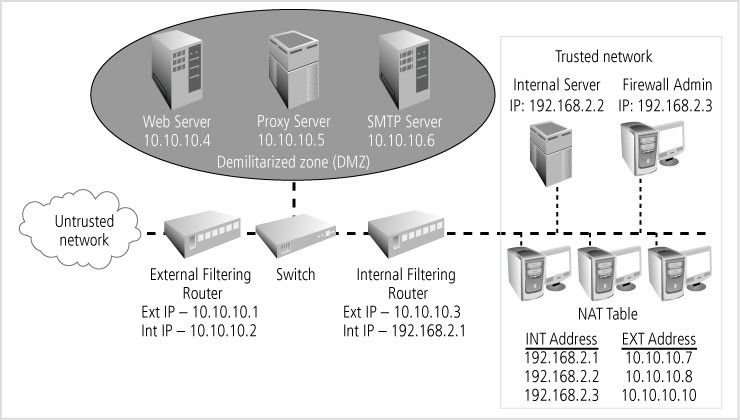
3. How many sets of rules do you need for this network diagram?
4.Traffic from the untrusted network to the trusted network is called _____________ traffic.
5. List the seven best practices for firewalls (A)
For each one, briefly describe why it is a best practice, that is, explain how this best practice protects the trusted network. (B)
Untrusted network Web Server Proxy Server SMTP Server 10.10.10.5 10.10. 10.6 10.10.10.4 Demilitarized zone (DMZ) External Filtering Switch nternal Filtering Router Router Ext IP-10, 10.10.1 Ext IP 10.10.10.3 Int IP 10.10.10.2 Int IP 192.168.2.1 Trusted network Internal Server Firewall Admin IP: 192.168.2.2 IP: 192.168.2.3 NAT Table NT Address EXT Address 192.168.2.1 10.10.10.7 192.168.2.2 10.10.10.8 192.168.2.3 0.10.10.10Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started