Answered step by step
Verified Expert Solution
Question
1 Approved Answer
2 . 3 Task 1 . 3 : Traceroute in python The objective of this task is to use Scapy to estimate the distance, in
Task : Traceroute in python
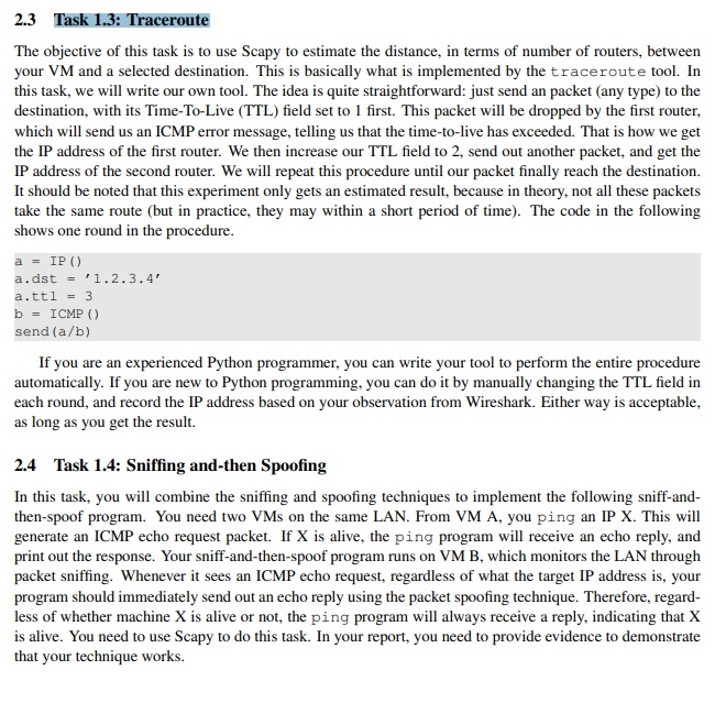
The objective of this task is to use Scapy to estimate the distance, in terms of number of routers, between
your VM and a selected destination. This is basically what is implemented by the traceroute tool. In
this task, we will write our own tool. The idea is quite straightforward: just send an packet any type to the
destination, with its TimeToLive TTL field set to first. This packet will be dropped by the first router,
which will send us an ICMP error message, telling us that the timetolive has exceeded. That is how we get
the IP address of the first router. We then increase our TTL field to send out another packet, and get the
IP address of the second router. We will repeat this procedure until our packet finally reach the destination.
It should be noted that this experiment only gets an estimated result, because in theory, not all these packets
take the same route but in practice, they may within a short period of time The code in the following
shows one round in the procedure.
adst
a
ICMP
send
If you are an experienced Python programmer, you can write your tool to perform the entire procedure
automatically. If you are new to Python programming, you can do it by manually changing the TTL field in
each round, and record the IP address based on your observation from Wireshark. Either way is acceptable,
as long as you get the result.
Task : Sniffing andthen Spoofing
In this task, you will combine the sniffing and spoofing techniques to implement the following sniffand
thenspoof program. You need two VMs on the same LAN. From VM A you ping an IP X This will
generate an ICMP echo request packet. If is alive, the ping program will receive an echo reply, and
print out the response. Your sniffandthenspoof program runs on VM B which monitors the LAN through
packet sniffing. Whenever it sees an ICMP echo request, regardless of what the target IP address is your
program should immediately send out an echo reply using the packet spoofing technique. Therefore, regard
less of whether machine is alive or not, the ping program will always receive a reply, indicating that
is alive. You need to use Scapy to do this task. In your report, you need to provide evidence to demonstrate
that your technique works.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


