Question
2. All the following questions are against the penetration scenario shown in Figure 1. In this penetration scenario, Mallory is a remote attacker who has
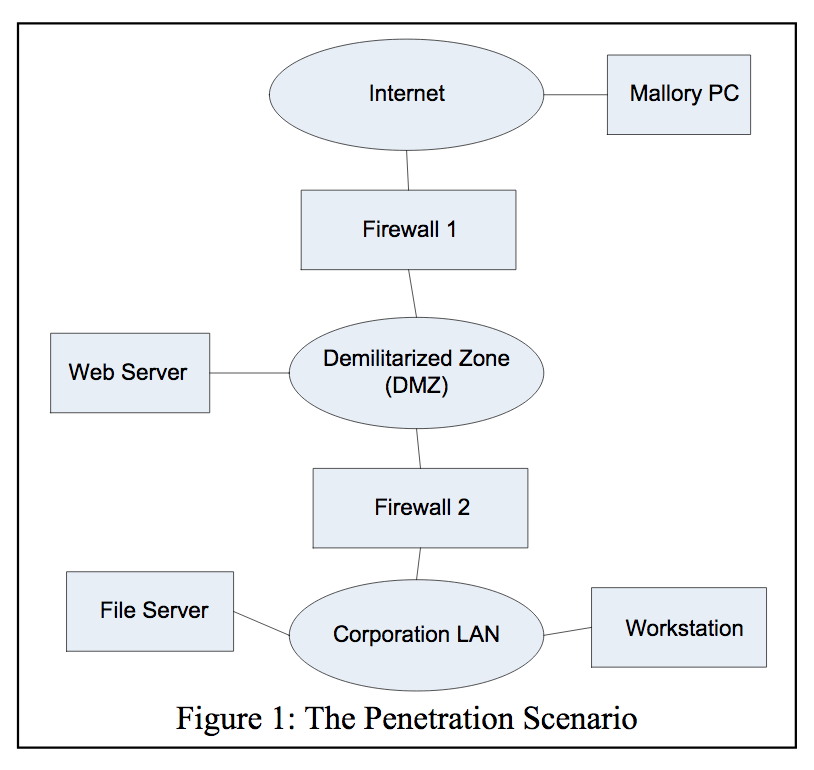
2. All the following questions are against the penetration scenario shown in Figure 1. In this penetration scenario,
Mallory is a remote attacker who has no user account of the corporation. The goal of Mallory is to gain root privilege on the Workstation.
2.1: Since Mallory knows nothing about the corporation, he will need to start with the reconnaissance step. In particular, since breaking into the internal Corporation LAN (see Figure 1) is much harder than breaking into the Web Server, Mallory will target the Web Server in this step. To do reconnaissance against the Web Server, Mallory will need to use a set of scanning tools. In particular, one of these scanning tools, when executed on Mallory PC, told Mallory that the Web Server was running Apache HTTP Server Version 2.0. What did the scanning tool/weapon do in order to collect such useful information? Please give a step-by-step explanation. (10 points)
2.2: When the reconnaissance step ends, Mallory knew that the Web Server httpd program had a buffer overflow bug (vulnerability). To exploit this vulnerability to break into the
Web Server, Mallory should take the Probe step and use a specific remote exploit tool. Which attack weapon would be used by Mallory? Which kind of attack packets will be
created and sent to the Web Server by this attack weapon? (10 points)
2.3: During the Toehold step, the buffer overflow bug was successfully exploited and Mallorys malicious code was executed on the Web Server. The malicious code can enable Mallory to remotely login into the Web Server. When Mallory remotely logins into the Web Server, what are the three most urgent things for Mallory to do? Why are they urgent? (10 points)
2.4: Next, Mallory wanted to break into the Fire Server inside Firewall 2. So Mallory would take the reconnaissance step and the Probe step again. The reconnaissance tool told Mallory that the File Server has a TCP port open to accept and process RPC requests. Since Mallory knew that many RPC server programs have buffer overflow bugs, he would probe this port. Please list all the possible attack weapons that could help Mallory probe the port; then please tell which attack weapon is the best one for this attacking purpose. (10 points)
2.5: After the Probe step succeeded, Mallory would gain root privilege on the File Server and be able to remotely login into the File Server. Lets assume Mallory was not ready at this moment to attack and break into the Workstation from the File Server. So he was worried that his attack traces could be detected and the RPC buffer overflow bug could be patched when he got ready to attack the Workstation. What could Mallory do to remove this concern? Please give a step- by-step answer. (10 points)
2.6: Now Mallory was ready to attack the Workstation from the File Server. In this stage, should Mallory use any monitoring tools? If so, what can these monitoring tools do and why are they helpful? (10 points)
2.7: When attacking the Workstation, the reconnaissance tools did not find any buffer overflow vulnerabilities. So Mallory could no longer send buffer overflow packets (or requests) to the Workstation. Now Mallory needed to do some other things. Please select all the useful ones from the attack weapons listed below and explain WHY. (10 points)
(a) packet sniffers; (b) spoofing; (c) password crackers; (d) denial-of-service; (e) virus; (f) worm (g) Malicious applets; (h) buffer overflow; (i) exploit bugs; (j) social engineering; (k) dumpster diving
2.8: After a while, Mallory was able to install a Trojan horse on the Workstation. Then he used the Trojan horse to help him steal the password of a non-root user account on the Workstation. Now Mallory was in which step of the seven penetration steps? What will Mallory do next on the Workstation? (10 points)
2.9: During the whole attack process from Mallory PC to the Workstation, password crackers can be useful in which steps and on which machines? (10 points)
Internet Mallory PC Firewall 1 Demilitarized Zone (DMZ) Web Server Firewall2 File Server Corporation LAN Workstation Figure 1: The Penetration ScenarioStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


