Answered step by step
Verified Expert Solution
Question
1 Approved Answer
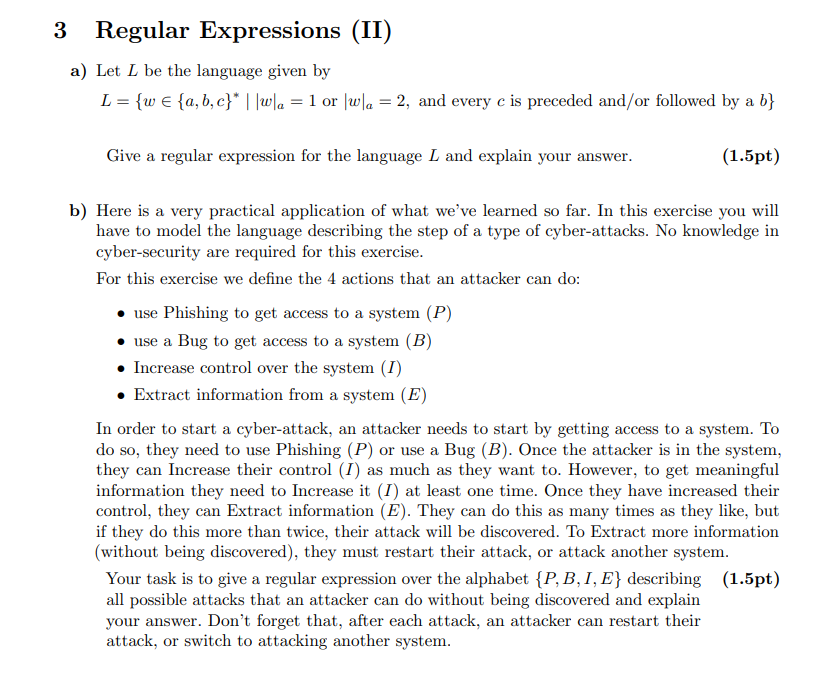
3 Regular Expressions ( II ) a ) Let L be the language given by L = { w i n { a , b
Regular Expressions II
a Let be the language given by
or and every is preceded andor followed by a :
Give a regular expression for the language and explain your answer.
b Here is a very practical application of what we've learned so far. In this exercise you will
have to model the language describing the step of a type of cyberattacks. No knowledge in
cybersecurity are required for this exercise.
For this exercise we define the actions that an attacker can do:
use Phishing to get access to a system
use a Bug to get access to a system
Increase control over the system
Extract information from a system
In order to start a cyberattack, an attacker needs to start by getting access to a system. To
do so they need to use Phishing or use a Bug Once the attacker is in the system,
they can Increase their control as much as they want to However, to get meaningful
information they need to Increase it at least one time. Once they have increased their
control, they can Extract information They can do this as many times as they like, but
if they do this more than twice, their attack will be discovered. To Extract more information
without being discovered they must restart their attack, or attack another system.
Your task is to give a regular expression over the alphabet I, describing
all possible attacks that an attacker can do without being discovered and explain
your answer. Don't forget that, after each attack, an attacker can restart their
attack, or switch to attacking another system.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started