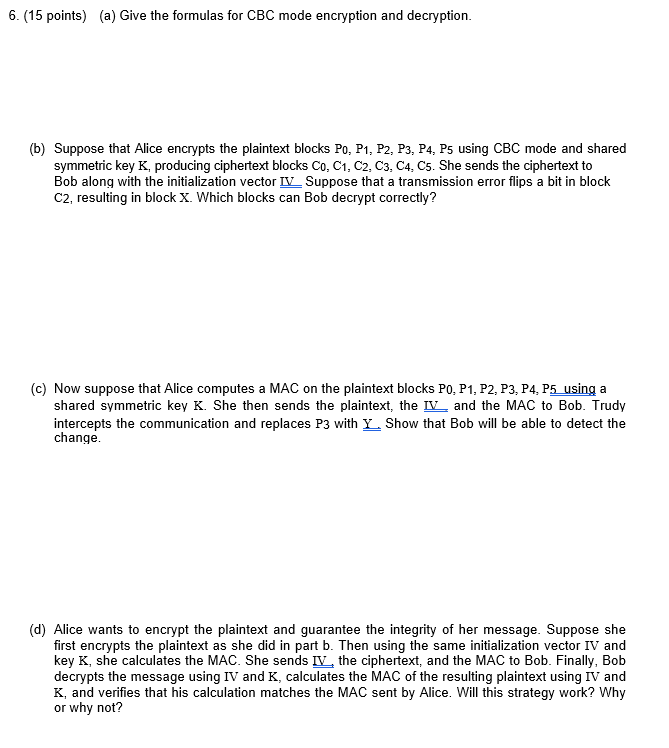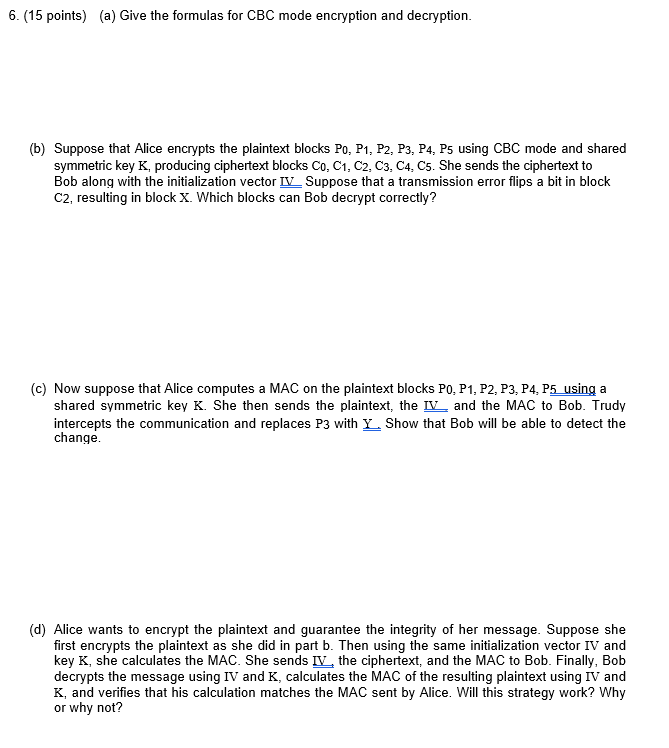
6. (15 points) (a) Give the formulas for CBC mode encryption and decryption. (b) Suppose that Alice encrypts the plaintext blocks Po, P1, P2, P3, P4, P5 using CBC mode and shared symmetric key K, producing ciphertext blocks Co, C1, C2, C3, C4, C5. She sends the ciphertext to Bob along with the initialization vector IV Suppose that a transmission error flips a bit in bloclk C2, resulting in block X. Which blocks can Bob decrypt correctly? (c) Now suppose that Alice computes a MAC on the plaintext blocks Po, P1, P2, P3, P4, P5 using a shared symmetric key K. She then sends the plaintext, the IVand the MAC to Bob. Trudy intercepts the communication and replaces P3 with Y Show that Bob will be able to detect the change (d) Alice wants to encrypt the plaintext and guarantee the integrity of her message. Suppose she first encrypts the plaintext as she did in part b. Then using the same initialization vector IV and key K, she calculates the MAC. She sends IV, the ciphertext, and the MAC to Bob. Finally, Bob decrypts the message using IV and K, calculates the MAC of the resulting plaintext using IV and K, and verifies that his calculation matches the MAC sent by Alice. Will this strategy work? Why or why not? 6. (15 points) (a) Give the formulas for CBC mode encryption and decryption. (b) Suppose that Alice encrypts the plaintext blocks Po, P1, P2, P3, P4, P5 using CBC mode and shared symmetric key K, producing ciphertext blocks Co, C1, C2, C3, C4, C5. She sends the ciphertext to Bob along with the initialization vector IV Suppose that a transmission error flips a bit in bloclk C2, resulting in block X. Which blocks can Bob decrypt correctly? (c) Now suppose that Alice computes a MAC on the plaintext blocks Po, P1, P2, P3, P4, P5 using a shared symmetric key K. She then sends the plaintext, the IVand the MAC to Bob. Trudy intercepts the communication and replaces P3 with Y Show that Bob will be able to detect the change (d) Alice wants to encrypt the plaintext and guarantee the integrity of her message. Suppose she first encrypts the plaintext as she did in part b. Then using the same initialization vector IV and key K, she calculates the MAC. She sends IV, the ciphertext, and the MAC to Bob. Finally, Bob decrypts the message using IV and K, calculates the MAC of the resulting plaintext using IV and K, and verifies that his calculation matches the MAC sent by Alice. Will this strategy work? Why or why not