Answered step by step
Verified Expert Solution
Question
1 Approved Answer
6339641 QUESTION 7 10 As part of network attack, port scanner, such as NMAP is for O information gathering O vulnerabilities analysis O launch of
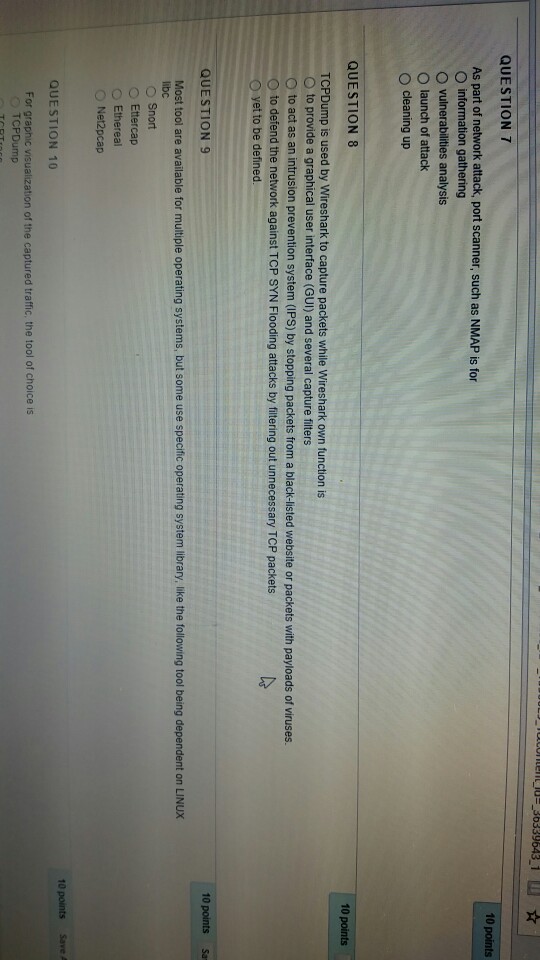
6339641 QUESTION 7 10 As part of network attack, port scanner, such as NMAP is for O information gathering O vulnerabilities analysis O launch of attack O cleaning up QUESTION 8 TCPDump is used by Wireshark to capture packets while Wireshark own function is O to provide a graphical user interface (GUI) and several capture filters O to act as an intrusion prevention system (IPS) by stopping packets from a black-listed website or packets with payloads of viruses. O to defend the network against TCP SYN Flooding attacks by filtering out unnecessary TCP packets yet to be defined. QUESTION 9 Most tool are available for multiple operating systems, but some use specific operating system library, like the following tool being dependent on LINUX libc O Snort O Ettercap ? Ethereal ? Net2pcap 10 points Save A QUESTION 10 For graphic visualization of the captured traffic, the tool of choice is TCPDump
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started