Answered step by step
Verified Expert Solution
Question
1 Approved Answer
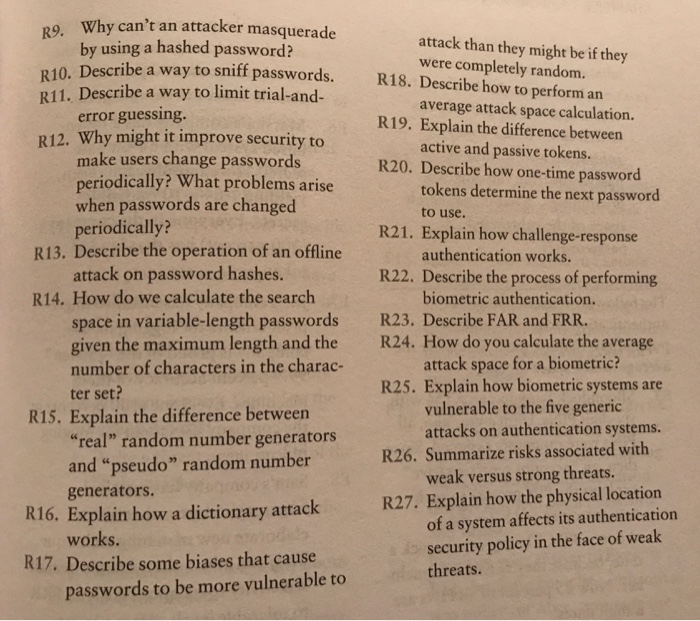
6.8.1 Review Questions R1. Explain the difference between R2. Describe the general steps taken R3. Identify and describe the three basic R4. Explain the role
 6.8.1 Review Questions R1. Explain the difference between R2. Describe the general steps taken R3. Identify and describe the three basic R4. Explain the role of hard to forge Describe the type of authentication environment examined in this chapter. R5. authentication and authorization. during the authentication process. authentication factors. information in authentication. Ro. Esplain the diffrences berwen to Is of threats described in this chapter. Describe the five basic attacks on authentication systems. Describe how password hashing works. R7. Give examples of such informa- R8. tion
6.8.1 Review Questions R1. Explain the difference between R2. Describe the general steps taken R3. Identify and describe the three basic R4. Explain the role of hard to forge Describe the type of authentication environment examined in this chapter. R5. authentication and authorization. during the authentication process. authentication factors. information in authentication. Ro. Esplain the diffrences berwen to Is of threats described in this chapter. Describe the five basic attacks on authentication systems. Describe how password hashing works. R7. Give examples of such informa- R8. tion
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started