 6(a)
6(a)
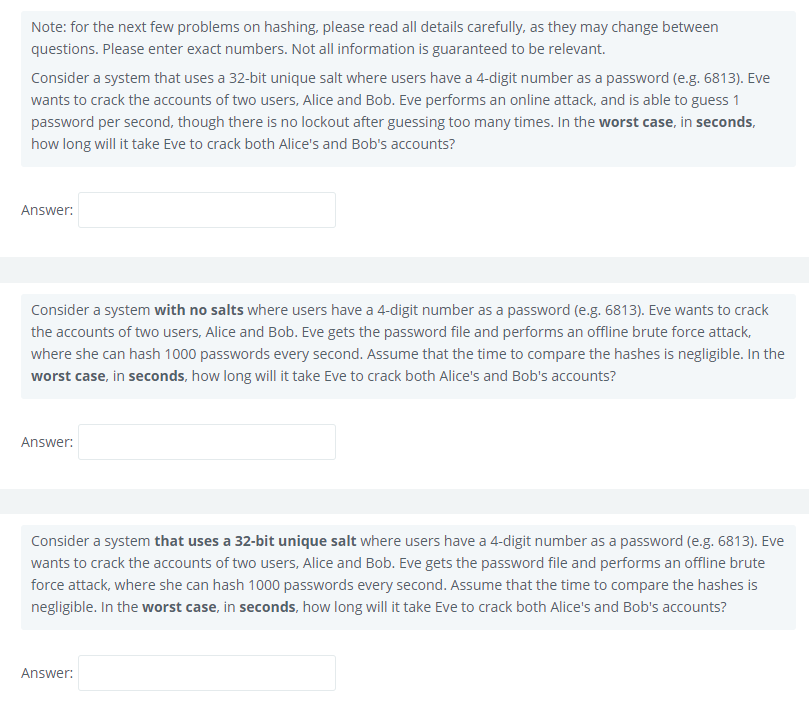
Note: for the next few problems on hashing, please read all details carefully, as they may change between questions. Please enter exact numbers. Not all information is guaranteed to be relevant.
Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve performs an online attack, and is able to guess 1 password per second, though there is no lockout after guessing too many times. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts?
Answer:
(b)
Consider a system with no salts where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts?
Answer:
(c)
Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts?
Answer: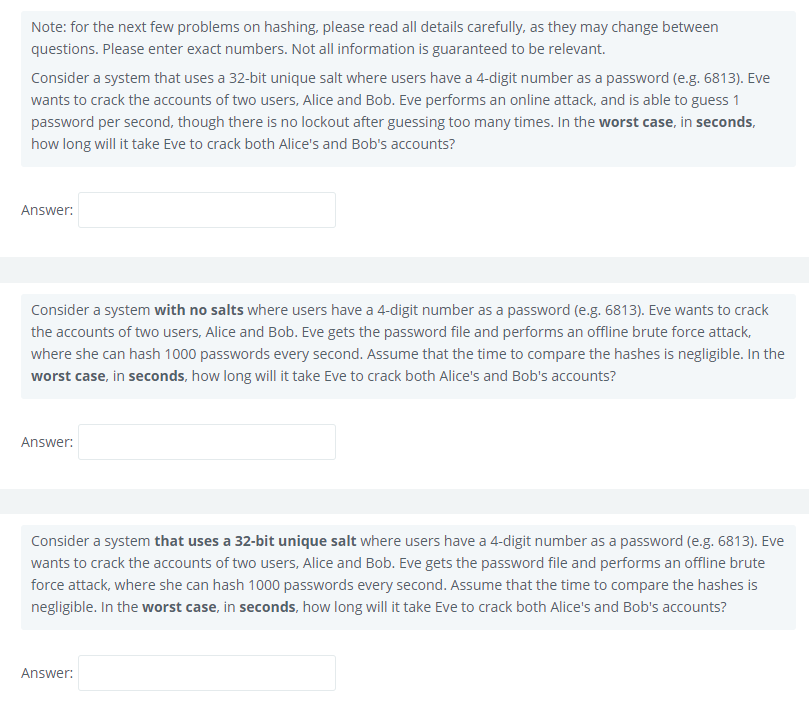
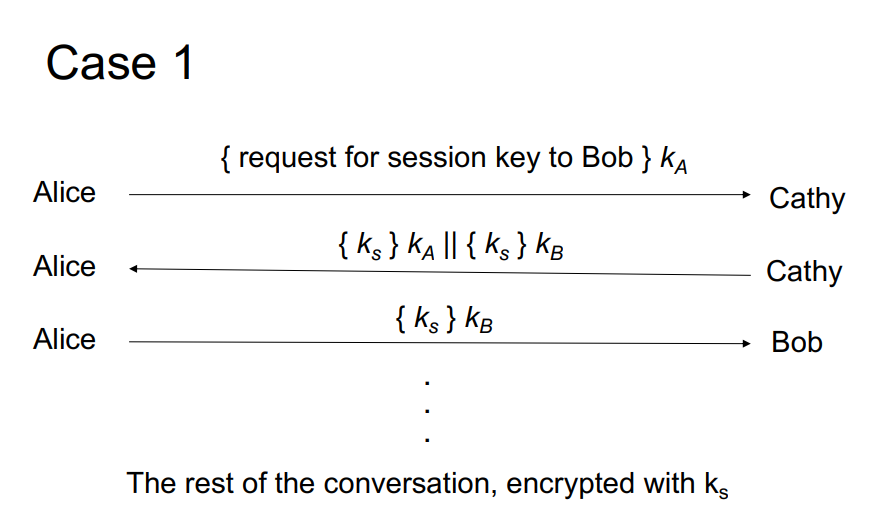
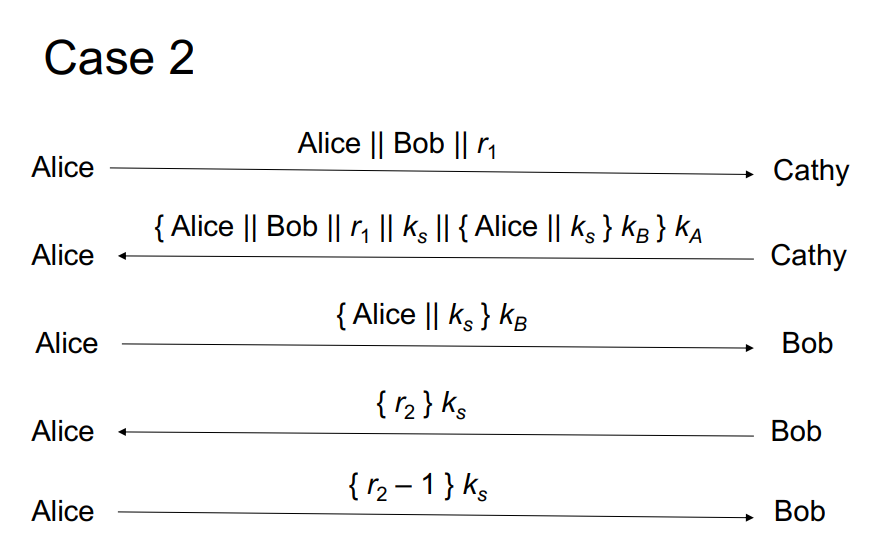
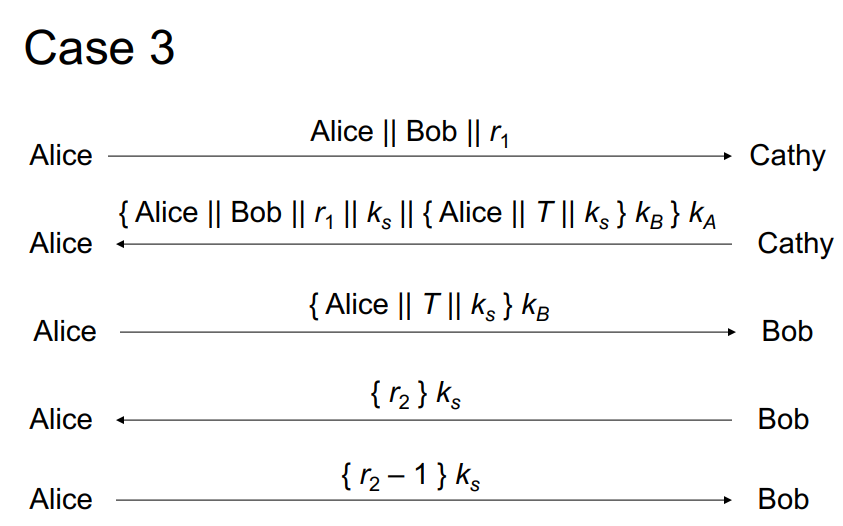
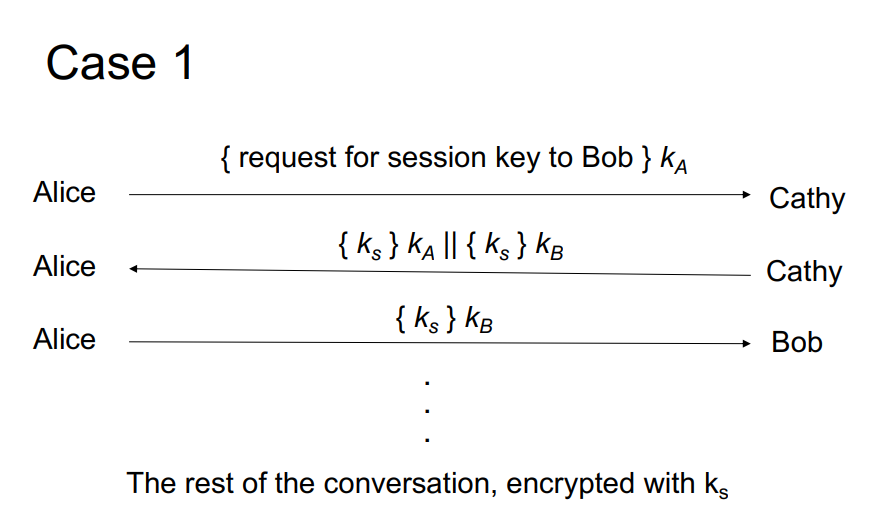
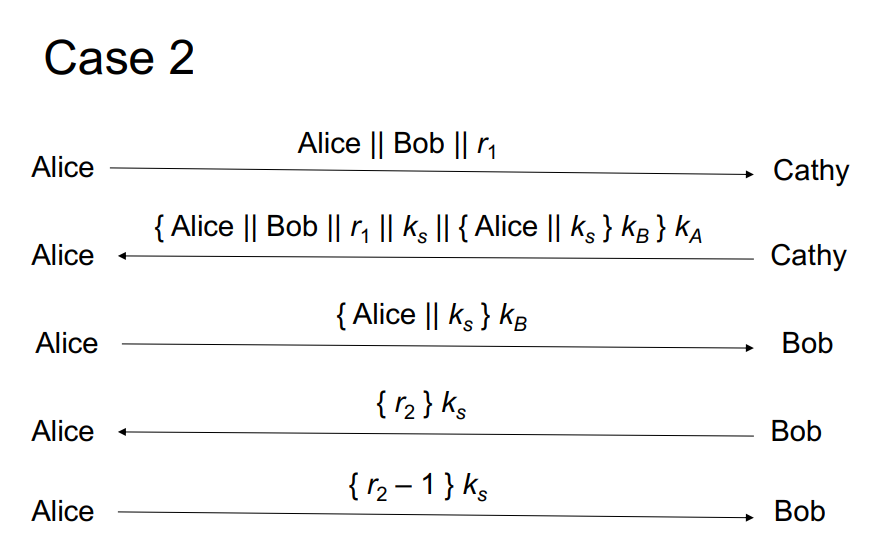
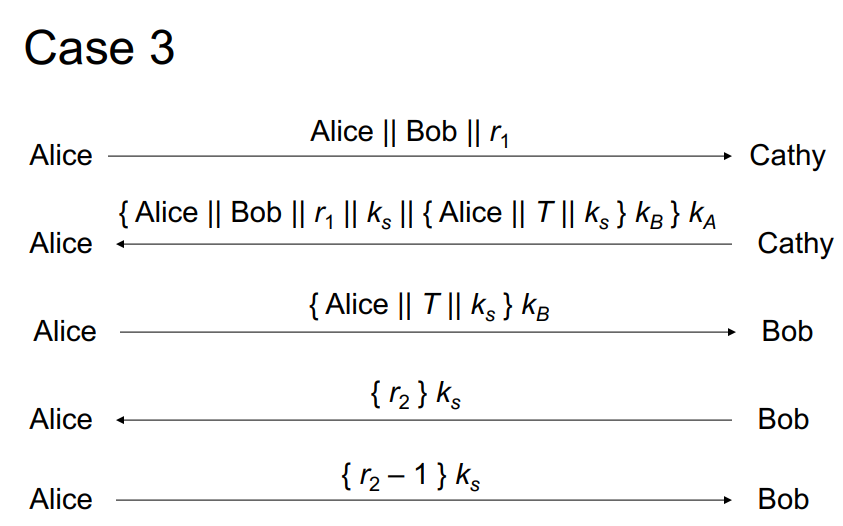
Case 1 { request for session key to Bob } ka Alice Cathy {ks } kall { ks } KB Alice Cathy Alice - {Ks} kB Bob The rest of the conversation, encrypted with ks Case 2 Alice || Bob || r1 Alice Cathy {Alice || Bob || 61 || ks Il {Alice || ks } ke} ka Alice + Cathy { Alice || ks } KB Alice Bob {r2} ks Alice Bob {r2-1}ks Alice Bob Case 3 Alice Alice || Bob || r1 Cathy {Alice || Bob || 61 || ks || {Alice || T || ks } k}ka Alice Cathy {Alice || T || ks } kg Alice Bob { r2}k Alice + Bob {12-1} ks Alice Bob Note: for the next few problems on hashing, please read all details carefully, as they may change between questions. Please enter exact numbers. Not all information is guaranteed to be relevant. Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve performs an online attack, and is able to guess 1 password per second, though there is no lockout after guessing too many times. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts? Answer: Consider a system with no salts where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts? Answer: Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts? Answer: Case 1 { request for session key to Bob } ka Alice Cathy {ks } kall { ks } KB Alice Cathy Alice - {Ks} kB Bob The rest of the conversation, encrypted with ks Case 2 Alice || Bob || r1 Alice Cathy {Alice || Bob || 61 || ks Il {Alice || ks } ke} ka Alice + Cathy { Alice || ks } KB Alice Bob {r2} ks Alice Bob {r2-1}ks Alice Bob Case 3 Alice Alice || Bob || r1 Cathy {Alice || Bob || 61 || ks || {Alice || T || ks } k}ka Alice Cathy {Alice || T || ks } kg Alice Bob { r2}k Alice + Bob {12-1} ks Alice Bob Note: for the next few problems on hashing, please read all details carefully, as they may change between questions. Please enter exact numbers. Not all information is guaranteed to be relevant. Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve performs an online attack, and is able to guess 1 password per second, though there is no lockout after guessing too many times. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts? Answer: Consider a system with no salts where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts? Answer: Consider a system that uses a 32-bit unique salt where users have a 4-digit number as a password (e.g. 6813). Eve wants to crack the accounts of two users, Alice and Bob. Eve gets the password file and performs an offline brute force attack, where she can hash 1000 passwords every second. Assume that the time to compare the hashes is negligible. In the worst case, in seconds, how long will it take Eve to crack both Alice's and Bob's accounts
 6(a)
6(a)