Answered step by step
Verified Expert Solution
Question
1 Approved Answer
A. Adding rules on the Victim to perform the following Allow secure shell (SSH) and FTP only from 192.168.0.4 the PLABCLIENT1 Allow any user
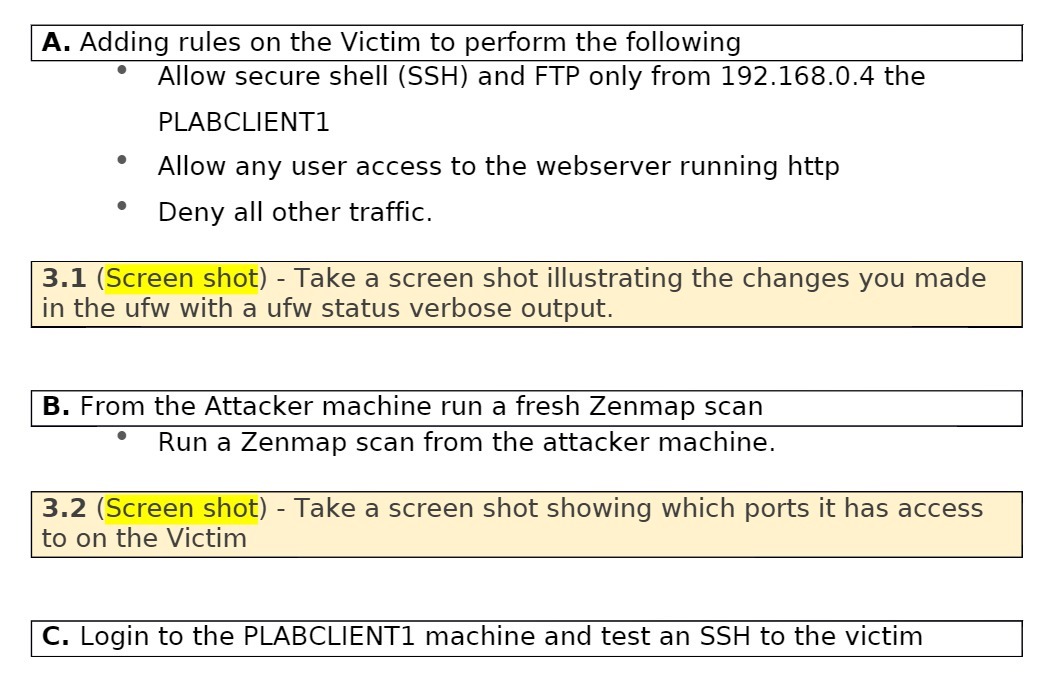
A. Adding rules on the Victim to perform the following Allow secure shell (SSH) and FTP only from 192.168.0.4 the PLABCLIENT1 Allow any user access to the webserver running http Deny all other traffic. 3.1 (Screen shot) - Take a screen shot illustrating the changes you made in the ufw with a ufw status verbose output. B. From the Attacker machine run a fresh Zenmap scan Run a Zenmap scan from the attacker machine. 3.2 (Screen shot) - Take a screen shot showing which ports it has access to on the Victim C. Login to the PLABCLIENT1 machine and test an SSH to the victim
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


