Answered step by step
Verified Expert Solution
Question
1 Approved Answer
a) Data leaks and database inconsistencies are two of the most common database vulnerabilities. Discuss TWO (2) basic security requirements of database systems to
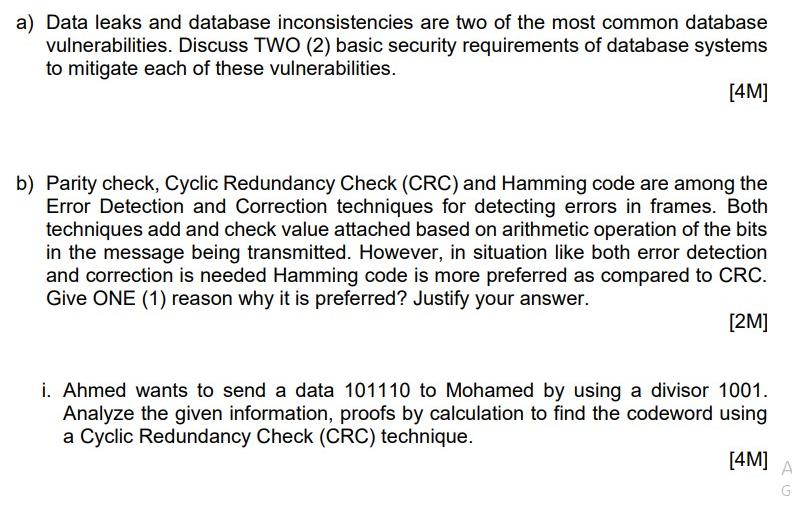
a) Data leaks and database inconsistencies are two of the most common database vulnerabilities. Discuss TWO (2) basic security requirements of database systems to mitigate each of these vulnerabilities. [4M] b) Parity check, Cyclic Redundancy Check (CRC) and Hamming code are among the Error Detection and Correction techniques for detecting errors in frames. Both techniques add and check value attached based on arithmetic operation of the bits in the message being transmitted. However, in situation like both error detection and correction is needed Hamming code is more preferred as compared to CRC. Give ONE (1) reason why it is preferred? Justify your answer. [2M] i. Ahmed wants to send a data 101110 to Mohamed by using a divisor 1001. Analyze the given information, proofs by calculation to find the codeword using a Cyclic Redundancy Check (CRC) technique. [4M] A G
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


