Answered step by step
Verified Expert Solution
Question
1 Approved Answer
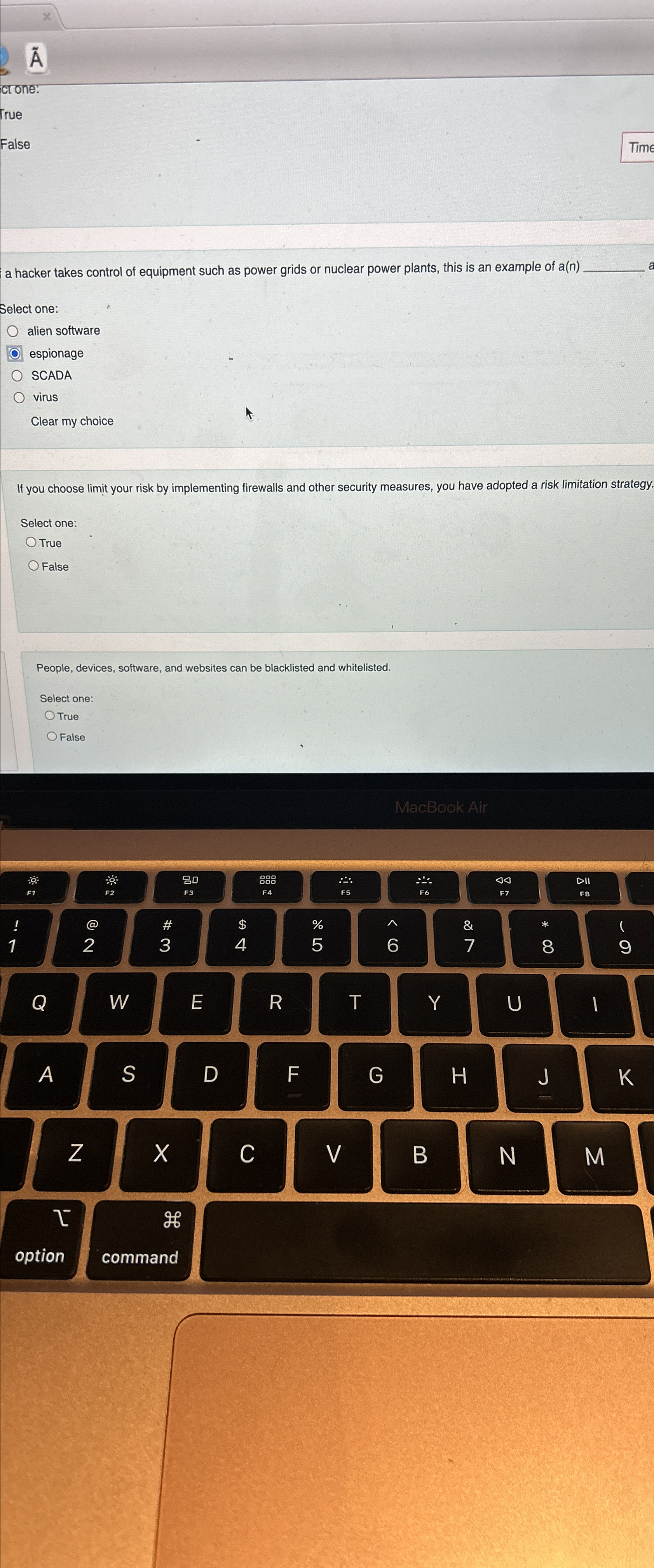
a hacker takes control of equipment such as power grids or nuclear power plants, this is an example of a ( n ) Select one:
a hacker takes control of equipment such as power grids or nuclear power plants, this is an example of an
Select one:
alien software
espionage
SCADA
virus
Clear my choice
If you choose limit your risk by implementing firewalls and other security measures, you have adopted a risk limitation strategy
Select one:
True
False
People, devices, software, and websites can be blacklisted and whitelisted.
Select one:
True
False
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started