Answered step by step
Verified Expert Solution
Question
1 Approved Answer
a table [ [ table [ [ Security ] , [ Strength ] ] , table [ [ Symmetric ] , [
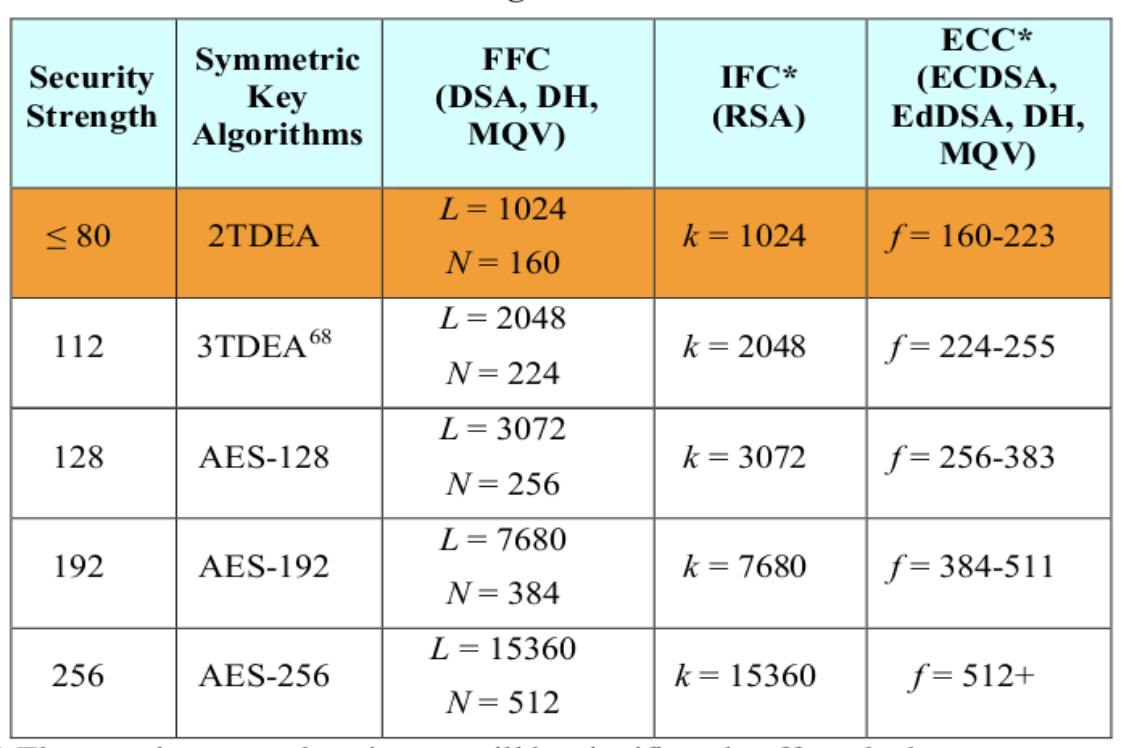
atabletableSecurityStrengthtableSymmetricKeyAlgorithmstableFFCDSA DHMQVtableIFCRSAtableECCECDSAEdDSA DHMQV TDEA,table Assume that a public key scheme that uses Elliptic Curve Cryptography with an n bit key can be broken in n steps. What keylength n is needed for this to be the same time as the worstcase time to brute force a bit key? Show the work and explain. Also how does this compare to the table image attached.
b A rough estimation of the time it takes to factor an nbit number of the type used by RSA is n over times the cube root of n Given this complexity, what key size n is needed for RSA to be as hard to break as the worstcase time to brute force a bit key? Also how does this compare to the attached table in the image.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started