Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Alice and Bob have decided to play the rock-paper-scissors game. In a single match, both sides choose one of the shapes at the same time
Alice and Bob have decided to play the rock-paper-scissors game. In a single match, both sides choose one of the shapes at the same time and the winner is determined according to certain rules. These rules are as follows: rock scissors, scissors paper and paper beats stone. These two players decided to play this game in the cryptography and security lesson based on the topics learned in the lesson. As a result, they decided to use the protocol given below. Alice's choice is represented by the letter a, and Bob's choice by the letter b. The H function is a known cryptographic hash function. (Once the protocol is running, Bob checks the H (a) value and both Alice and Bob have learned the winner.) (Note that this game has a short playing time and should be played without long waiting times like chess.)
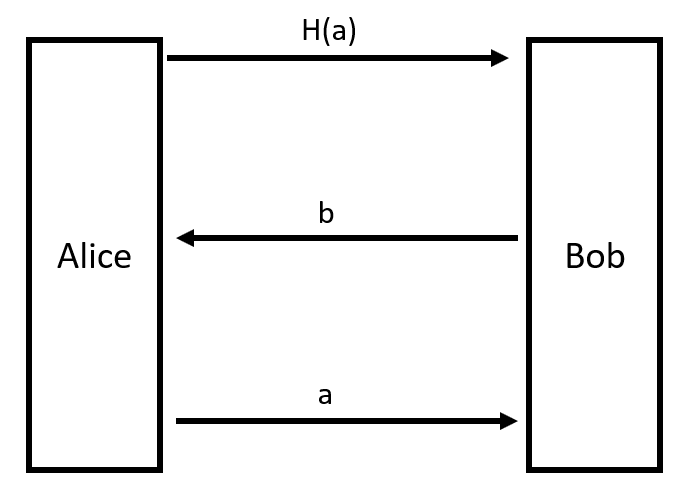
a) Discuss the weakness (s) of this protocol based on players' cheating in the game. b) What changes should be made to the protocol to correct this weakness? (Note: Without using a third party and public key encryption.)H(a) b Alice Bob a
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started