Question: all 46. Which kind of security attack uses a software agent between client and servers that records transactions, then modifies data and sends them to
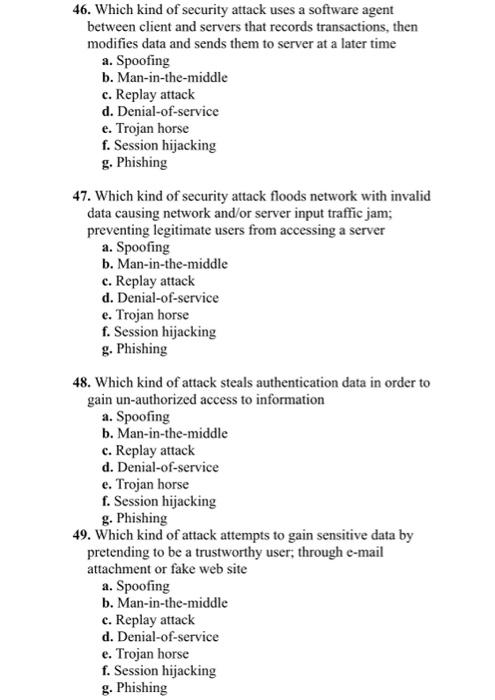
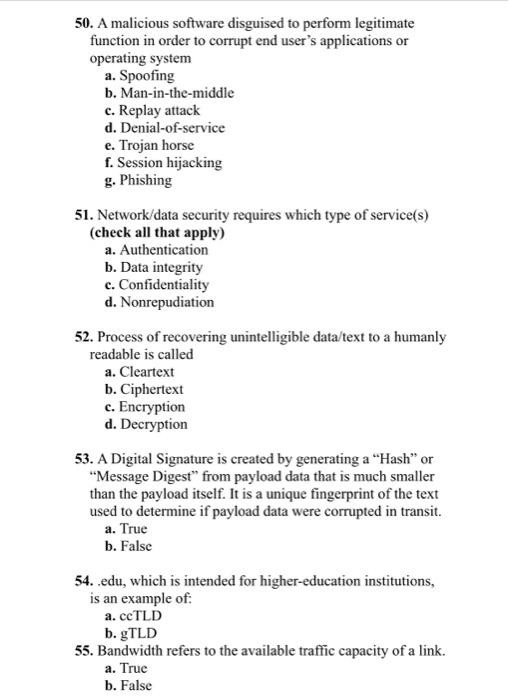
46. Which kind of security attack uses a software agent between client and servers that records transactions, then modifies data and sends them to server at a later time a. Spoofing b. Man-in-the-middle c. Replay attack d. Denial-of-service e. Trojan horse f. Session hijacking g. Phishing 47. Which kind of security attack floods network with invalid data causing network and/or server input traffic jam; preventing legitimate users from accessing a server a. Spoofing b. Man-in-the-middle c. Replay attack d. Denial-of-service e. Trojan horse f. Session hijacking g. Phishing 48. Which kind of attack steals authentication data in order to gain un-authorized access to information a. Spoofing b. Man-in-the-middle c. Replay attack d. Denial-of-service e. Trojan horse f. Session hijacking g. Phishing 49. Which kind of attack attempts to gain sensitive data by pretending to be a trustworthy user; through e-mail attachment or fake web site a. Spoofing b. Man-in-the-middle c. Replay attack d. Denial-of-service e. Trojan horse f. Session hijacking g. Phishing 50. A malicious software disguised to perform legitimate function in order to corrupt end user's applications or operating system a. Spoofing b. Man-in-the-middle c. Replay attack d. Denial-of-service e. Trojan horse f. Session hijacking g. Phishing 51. Network/data security requires which type of service(s) (check all that apply) a. Authentication b. Data integrity c. Confidentiality d. Nonrepudiation 52. Process of recovering unintelligible data/text to a humanly readable is called a. Cleartext b. Ciphertext c. Encryption d. Decryption 53. A Digital Signature is created by generating a "Hash" or "Message Digest" from payload data that is much smaller than the payload itself. It is a unique fingerprint of the text used to determine if payload data were corrupted in transit. a. True b. False 54. edu, which is intended for higher-education institutions, is an example of: a. ccTLD b. gTLD 55. Bandwidth refers to the available traffic capacity of a link. a. True b. False
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


