Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Analyze the following scheme and answer the questions . a. What security objectives this scheme provide? b. What pair of keys are used to ensure
Analyze the following scheme and answer the questions .
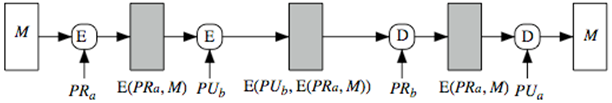
a. What security objectives this scheme provide?
b. What pair of keys are used to ensure confidentiality
c. What pair of keys are used to ensure authentication of the sender ?
d. Suppose a hacker be able to intercept E(PRa,M), can he retrieve M ?
e. Can you simplify the scheme, if we do not need confidentiality ? Only the authentication of the sender is needed.
E E D D M PRA E(Pra, M) PU, E(PU), E(PR, M) PRE(PR, M) PUAStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


