Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Answer true and false and give youre reasoning Part B: True/False 1. The A in the CIA triad stands for authenticity. 2. Computer security is
Answer true and false and give youre reasoning 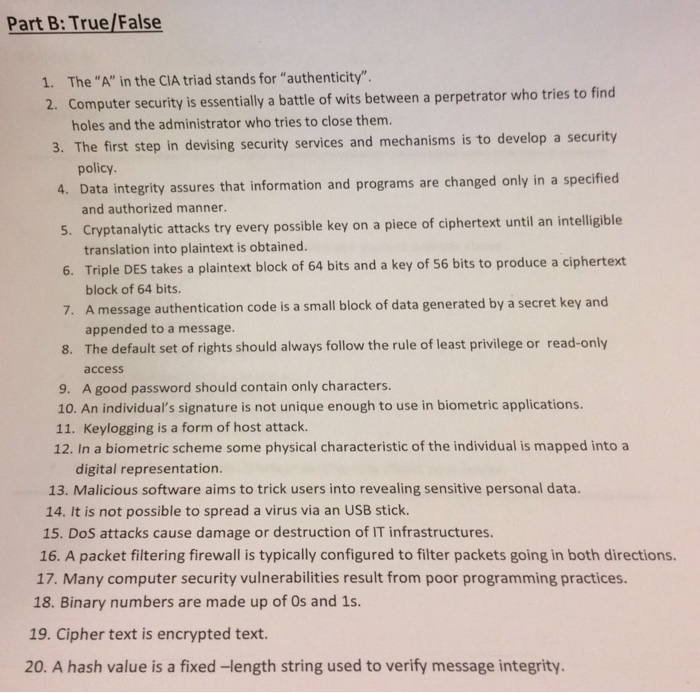
Part B: True/False 1. The "A" in the CIA triad stands for "authenticity". 2. Computer security is essentially a battle of wits between a perpetrator who tries to find holes and the administrator who tries to close them. 3. The first step in devising securit y services and mechanisms is to develop a security policy. 4. Data integrity assures that information and programs are changed only in a specified and authorized manner. 5. Cryptanalytic attacks try every possible key on a piece of ciphertext until an intelligible translation into plaintext is obtained. 6. Triple DES takes a plaintext block of 64 bits and a key of 56 bits to produce a ciphertext block of 64 bits. A message authentication code is a small block of data generated by a secret key and appended to a message. 7. 8. The default set of rights should always follow the rule of least privilege or read-only access 9. A good password should contain only characters. 10. An individual's signature is not unique enough to use in biometric applications. 11. Keylogging is a form of host attack. 12. In a biometric scheme some physical characteristic of the individual is mapped into a digital representation. 13. Malicious software aims to trick users into revealing sensitive personal data. 14. It is not possible to spread a virus via an USB stick. 15. DoS attacks cause damage or destruction of IT infrastructures. 16. A packet filtering firewall is typically configured to filter packets going in both directions. 17. Many computer security vulnerabilities result from poor programming practices. 18. Binary numbers are made up of Os and 1s. 19. Cipher text is encrypted text. 20. A hash value is a fixed-length string used to verify message integrity 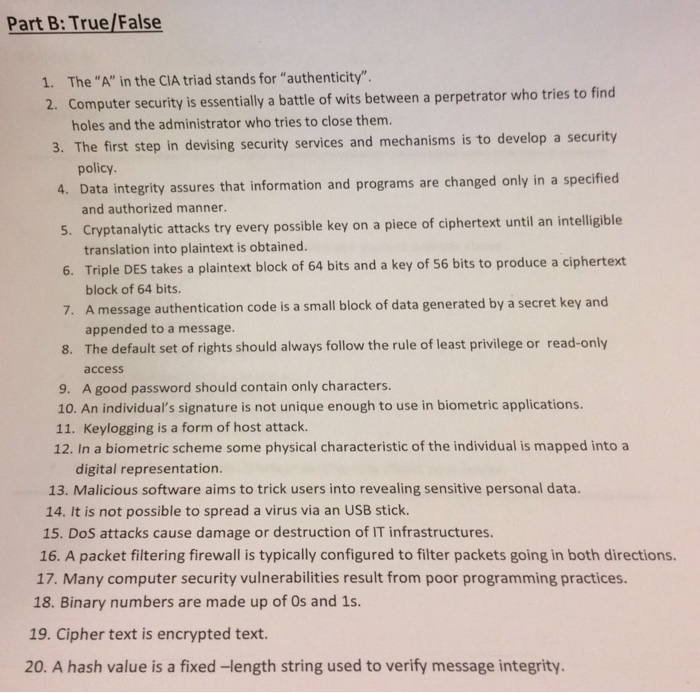
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started