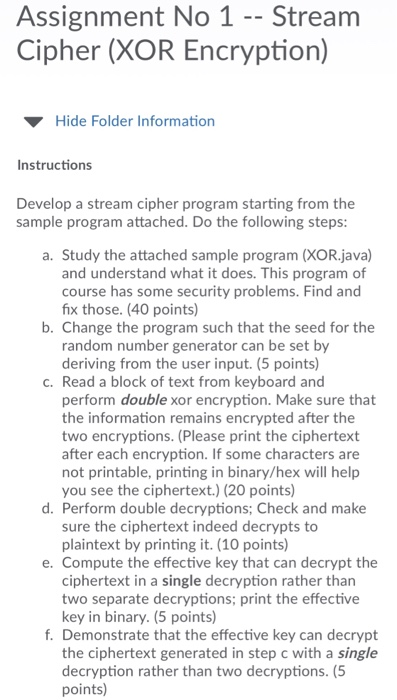
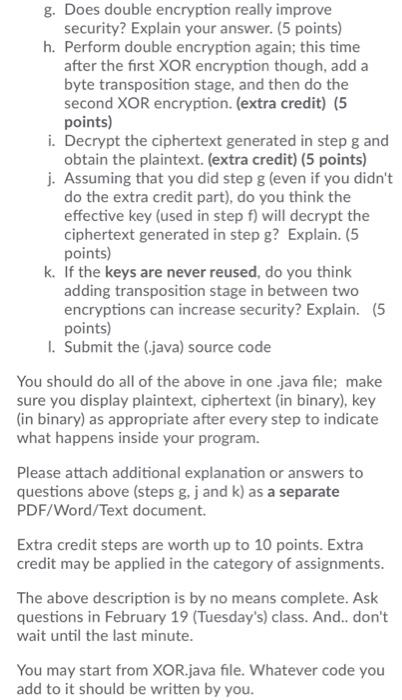
Assignment No 1 -- Stream Cipher (XOR Encryption) Hide Folder Information Instructions Develop a stream cipher program starting from the sample program attached. Do the following steps a. Study the attached sample program (XOR.java) and understand what it does. This program of course has some security problems. Find and fix those. (40 points) b. Change the program such that the seed for the random number generator can be set by deriving from the user input. (5 points) c. Read a block of text from keyboard and perform double xor encryption. Make sure that the information remains encrypted after the two encryptions. (Please print the ciphertext after each encryption. If some characters are not printable, printing in binary/hex will help you see the ciphertext.) (20 points) d. Perform double decryptions; Check and make sure the ciphertext indeed decrypts to plaintext by printing it. (10 points) e. Compute the effective key that can decrypt the ciphertext in a single decryption rather than two separate decryptions; print the effective key in binary. (5 points) f. Demonstrate that the effective key can decrypt the ciphertext generated in step c with a single decryption rather than two decryptions. (5 points) g. Does double encryption really improve security? Explain your answer. (5 points) h. Perform double encryption again; this time after the first XOR encryption though, add a byte transposition stage, and then do the second XOR encryption. (extra credit) (5 points) i. Decrypt the ciphertext generated in step g and obtain the plaintext. (extra credit) (5 points) j. Assuming that you did step g (even if you didn't do the extra credit part), do you think the effective key (used in step f) will decrypt the ciphertext generated in step g? Explain. (5 points) k. If the keys are never reused, do you think adding transposition stage in between two encryptions can increase security? Explain. points) (5 I. Submit the (java) source code You should do all of the above in one .java file; make sure you display plaintext, ciphertext (in binary), key (in binary) as appropriate after every step to indicate what happens inside your program. Please attach additional explanation or answers to questions above (steps g, j and k) as a separate PDF/Word/Text document. Extra credit steps are worth up to 10 points. Extra credit may be applied in the category of assignments The above description is by no means complete. Ask questions in February 19 (Tuesday's) class. And.. don't wait until the last minute You may start from XOR.java file. Whatever code you add to it should be written by you. Assignment No 1 -- Stream Cipher (XOR Encryption) Hide Folder Information Instructions Develop a stream cipher program starting from the sample program attached. Do the following steps a. Study the attached sample program (XOR.java) and understand what it does. This program of course has some security problems. Find and fix those. (40 points) b. Change the program such that the seed for the random number generator can be set by deriving from the user input. (5 points) c. Read a block of text from keyboard and perform double xor encryption. Make sure that the information remains encrypted after the two encryptions. (Please print the ciphertext after each encryption. If some characters are not printable, printing in binary/hex will help you see the ciphertext.) (20 points) d. Perform double decryptions; Check and make sure the ciphertext indeed decrypts to plaintext by printing it. (10 points) e. Compute the effective key that can decrypt the ciphertext in a single decryption rather than two separate decryptions; print the effective key in binary. (5 points) f. Demonstrate that the effective key can decrypt the ciphertext generated in step c with a single decryption rather than two decryptions. (5 points) g. Does double encryption really improve security? Explain your answer. (5 points) h. Perform double encryption again; this time after the first XOR encryption though, add a byte transposition stage, and then do the second XOR encryption. (extra credit) (5 points) i. Decrypt the ciphertext generated in step g and obtain the plaintext. (extra credit) (5 points) j. Assuming that you did step g (even if you didn't do the extra credit part), do you think the effective key (used in step f) will decrypt the ciphertext generated in step g? Explain. (5 points) k. If the keys are never reused, do you think adding transposition stage in between two encryptions can increase security? Explain. points) (5 I. Submit the (java) source code You should do all of the above in one .java file; make sure you display plaintext, ciphertext (in binary), key (in binary) as appropriate after every step to indicate what happens inside your program. Please attach additional explanation or answers to questions above (steps g, j and k) as a separate PDF/Word/Text document. Extra credit steps are worth up to 10 points. Extra credit may be applied in the category of assignments The above description is by no means complete. Ask questions in February 19 (Tuesday's) class. And.. don't wait until the last minute You may start from XOR.java file. Whatever code you add to it should be written by you