Question: Assume that the Selective Repeat-ARQ protocol is being used for communication between a source and a destination station. Assume that the transmission rate is
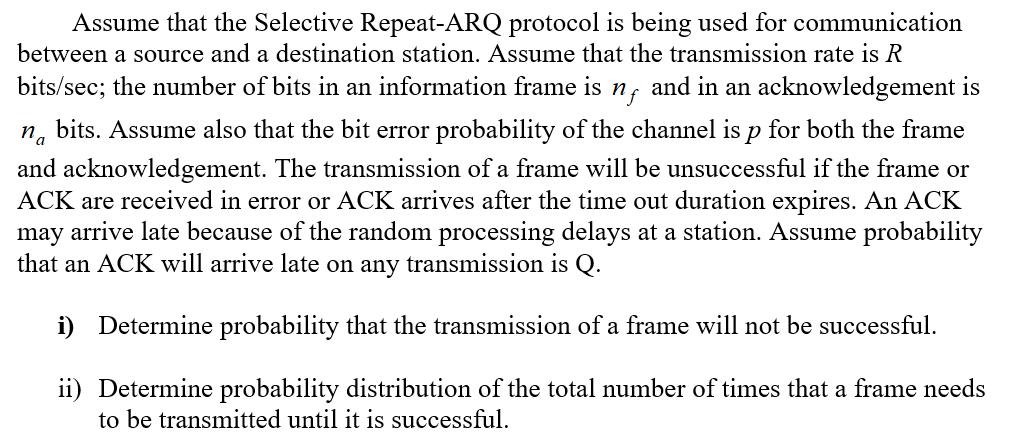
Assume that the Selective Repeat-ARQ protocol is being used for communication between a source and a destination station. Assume that the transmission rate is R bits/sec; the number of bits in an information frame is n, and in an acknowledgement is na bits. Assume also that the bit error probability of the channel is p for both the frame and acknowledgement. The transmission of a frame will be unsuccessful if the frame or ACK are received in error or ACK arrives after the time out duration expires. An ACK may arrive late because of the random processing delays at a station. Assume probability that an ACK will arrive late on any transmission is Q. i) Determine probability that the transmission of a frame will not be successful. ii) Determine probability distribution of the total number of times that a frame needs to be transmitted until it is successful. Assume that the Selective Repeat-ARQ protocol is being used for communication between a source and a destination station. Assume that the transmission rate is R bits/sec; the number of bits in an information frame is n, and in an acknowledgement is na bits. Assume also that the bit error probability of the channel is p for both the frame and acknowledgement. The transmission of a frame will be unsuccessful if the frame or ACK are received in error or ACK arrives after the time out duration expires. An ACK may arrive late because of the random processing delays at a station. Assume probability that an ACK will arrive late on any transmission is Q. i) Determine probability that the transmission of a frame will not be successful. ii) Determine probability distribution of the total number of times that a frame needs to be transmitted until it is successful.
Step by Step Solution
There are 3 Steps involved in it
address resolution protocol is a communication protocol used for discover... View full answer

Get step-by-step solutions from verified subject matter experts


