Answered step by step
Verified Expert Solution
Question
1 Approved Answer
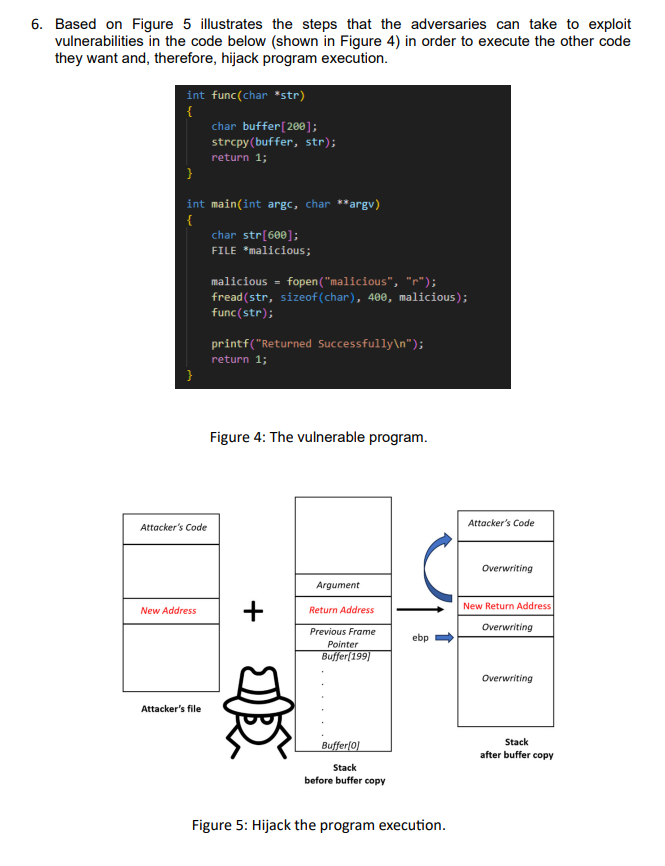
Based on Figure 5 illustrates the steps that the adversaries can take to exploit vulnerabilities in the code below ( shown in Figure 4 )
Based on Figure illustrates the steps that the adversaries can take to exploit
vulnerabilities in the code below shown in Figure in order to execute the other code
they want and, therefore, hijack program execution.
int funcchar str
char buffer;
strcpybuffer str;
return ;
int mainint argc, char argv
char str ;
FILE malicious;
malicious fopenmaliciousr;
freadstr sizeofchar malicious;
funcstr;
printfReturned Successfully
;
return ;
Figure : The vulnerable program.
Attacker's file
Stack
Stack
after buffer copy
before buffer copy
Figure : Hijack the program execution.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started