Question
Calculate the Window of Vulnerability You are reviewing the security status for a small Microsoft workgroup LAN. The workgroup contains many distinct separations in the
Calculate the Window of Vulnerability
You are reviewing the security status for a small Microsoft workgroup LAN. The workgroup contains many distinct separations in the network determined by group memberships. An example of the network divisions is as follows:
Windows laptops: Traveling salespeople, remote suppliers, branch offices
Windows desktops: Accounting group, developer group, customer service group
Windows servers: Administrative server, Microsoft SharePoint server, Server Message Block (SMB) server.
A security breach has been identified in which the SMB server was accessed by an unauthorized user due to a security hole. The hole was detected by the server software manufacturer the previous day. A patch will be available within three days. The LAN administrator needs at least one week to download, test, and install the patch. Calculate the WoV for the SMB server.
Window of Vulnerability
Vulnerability labels a condition or a set of conditions that make weakness in systems or networks that can potentially be manipulated. Think of vulnerability as the susceptibility of a system or network to be attacked and possibly damaged or disrupted. Vulnerabilities take many forms:
Easily guessable logon passwords
Poorly configured access controls
Exploitable programming flaws
Incorrect security implementations
Non-exploitable disruptive design flaws, such as denial of service (DoS)
Undocumented maintenance or debugging backdoors in software or systems
All of these problems and many others can exist simultaneously across numerous systems and devices.
Threats, risks, and vulnerabilities negatively impact the confidentiality, integrity, and availability (C-I-A) triad. Confidentiality is breached when an attacker discloses private information, integrity is broken when an attacker modifies privileged data, and availability is ruined when an attacker successfully denies service to a mission-critical resource.
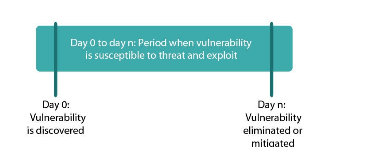
The length of time these vulnerabilities are present creates a window of vulnerability (WoV), the period within which defensive measures are reduced, compromised, or lacking. The WoV is the gap in time a workstation is exposed to a known vulnerability until it is patched. It also includes the time taken to create, publish, and finally apply a fix to the vulnerability. Problems arise as fixes can be disruptive to business operations and the delay between discovering and patching a hole leaves sufficient time for an attacker to intrude.
At any given time, a system or network will potentially have several overlapping WoVs, not all of which may be immediately identified. Remember, not all vulnerabilities are exploitable. Some exploits cause disruption such as DoS, while others may expose sensitive information or allow an attacker to take control.
Day to day n: Period when vulnerability is susceptible to threat and exploit Day 0: Vulnerability is discovered Day n: Vulnerability eliminated or mitigatedStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started