Question: CHAPTER 2 NETWORK MODELS 47 Another model that defines protocol layering is the Open Systems Interconnection (OSI) model. Two layers in the OSI model,
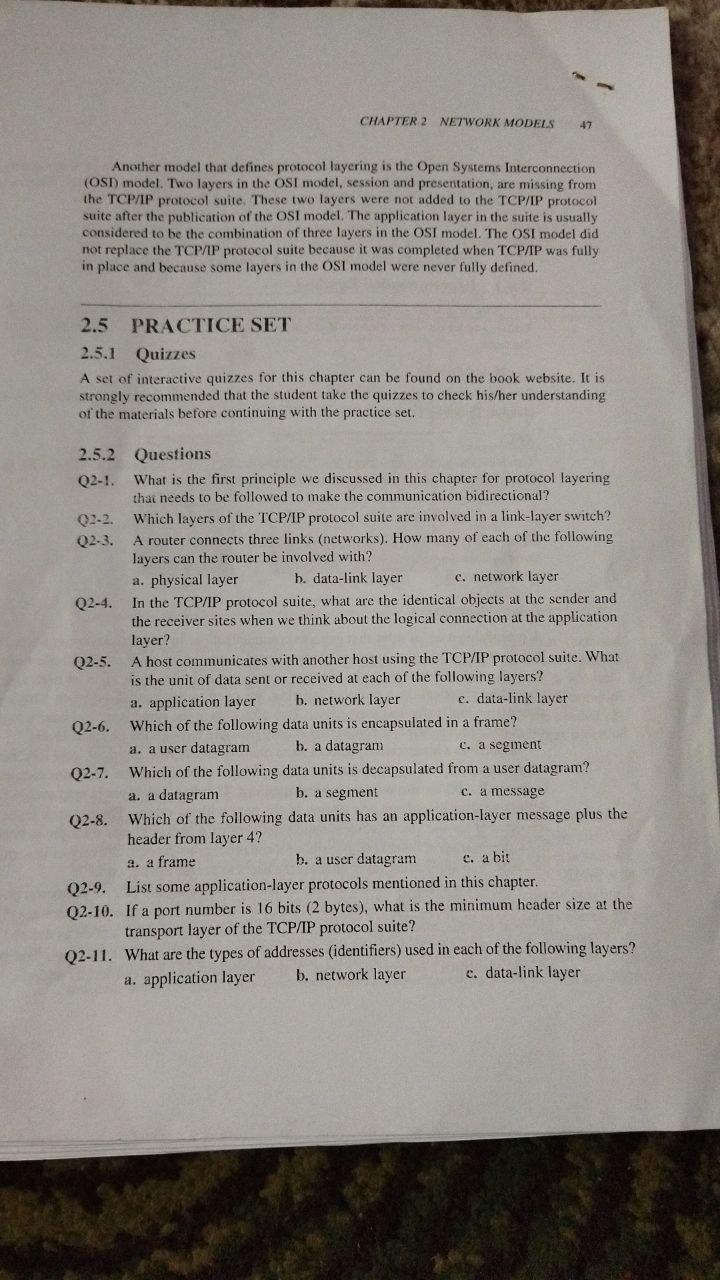
CHAPTER 2 NETWORK MODELS 47 Another model that defines protocol layering is the Open Systems Interconnection (OSI) model. Two layers in the OSI model, session and presentation, are missing from the TCP/IP protocol suite. These two layers were not added to the TCP/IP protocol suite after the publication of the OSI model. The application layer in the suite is usually considered to be the combination of three layers in the OSI model. The OSI model did not replace the TCP/IP protocol suite because it was completed when TCPAP was fully in place and because some layers in the OSI model were never fully defined. 2.5 PRACTICE SET 2.5.1 Quizzes A set of interactive quizzes for this chapter can be found on the book website, It is strongly recommended that the student take the quizzes to check his/her understanding of the materials before continuing with the practice set. 2.5.2 Questions What is the first principle we discussed in this chapter for protocol layering that needs to be followed to make the communication bidirectional? Q2-1. Which layers of the TCP/IP protocol suite are involved in a link-layer switch? A router connects three links (networks). How many of each of the following layers can the router be involved with? Q2-2. Q2-3. a. physical layer b. data-link layer c. network layer Q2-4. In the TCP/IP protocol suite, what are the identical objects at the sender and the receiver sites when we think about the logical connection at the application layer? A host communicates with another host using the TCP/IP protocol suite. What is the unit of data sent or received at each of the following layers? b. network layer Q2-5. a. application layer e. data-link layer Which of the following data units is encapsulated in a frame? b. a datagram Q2-6. a. a user datagram c. a segment Which of the following data units is decapsulated from a user datagram? b. a segment Q2-7. a. a datagram c. a message Q2-8. Which of the following data units has an application-layer message plus the header from layer 4? a. a frame b. a user datagram c. a bit Q2-9. List some application-layer protocols mentioned in this chapter. Q2-10. If a port number is 16 bits (2 bytes), what is the minimum header size at the transport layer of the TCP/IP protocol suite? Q2-11. What are the types of addresses (identifiers) used in each of the following layers? b. network layer a. application layer e. data-link layer
Step by Step Solution
3.38 Rating (154 Votes )
There are 3 Steps involved in it
Solutiou2 a data liuk layer are invelved u a linh layer kwitch 23 The nouter im... View full answer

Get step-by-step solutions from verified subject matter experts


