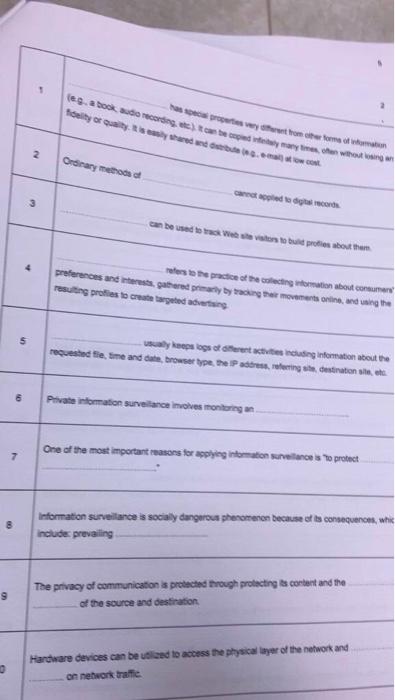
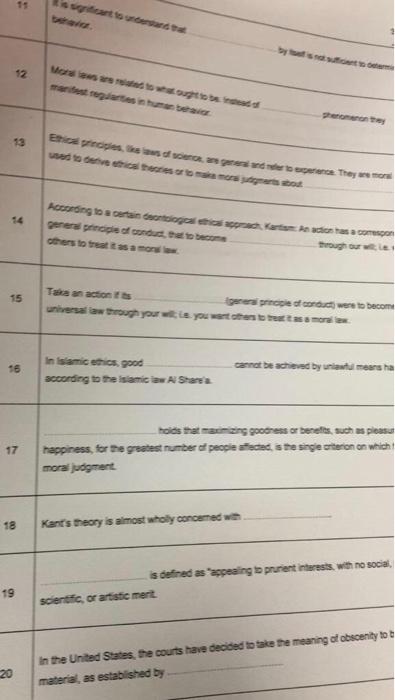
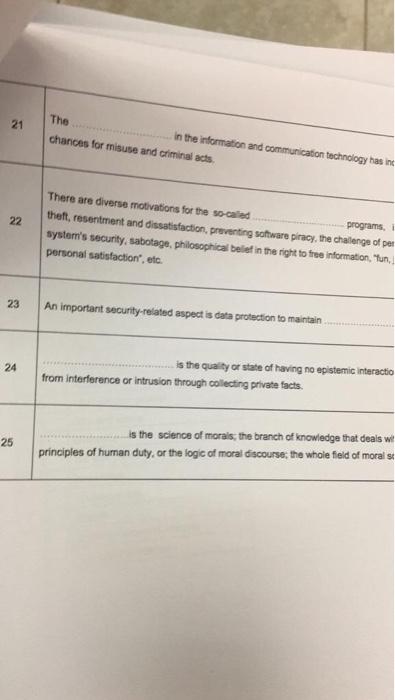
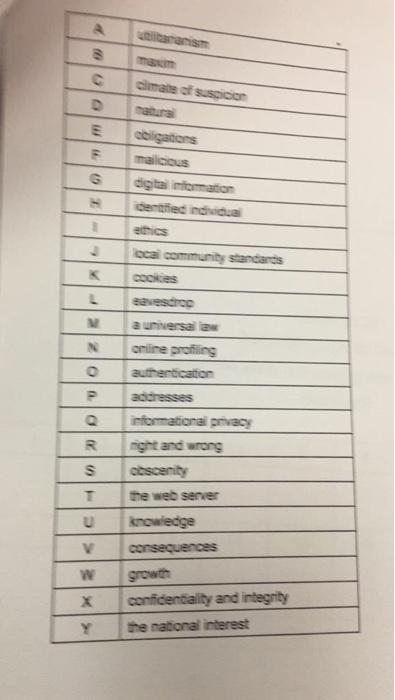
a book woco temayehen without losingan 5 Tality of Quality is there we has wychwsthom der formato 2. Ordinary methods care led to move can be used to wait to turbout them es to the practice of the acting nation about consumer preferences and interests gathered primary by anger movements online and wing the resulting profiles to create targeted ting 5 ways logs oor te ding information about the requested Sieme and browser type, the IP addressing destinations et 6 Private information surveillance moves monitoring One of the most important reasons for applying into vance to protect 7 8 Information surveillances socialy dangerous phenomenon because of its consequences, whic include prevailing The privacy of communication is protected through protecting as content and the of the source and destination Hardware devices can be ubland to access the physical layer of the network and on network trafic 15 12 manifest regartib groente rice, aws of someone. They were wted to deveria terestro According to a certain ortage Kartodiaco gerens principle of conduct that to become others to trust it as a mod 15 genera principle of conduct were to become universal law through your you want to tamo 16 In samicetics, good according to the Islamic law A Share carnet de schend by unit means ha 17 les mans press or benefits, such as please happiness, for the greatest number of people steeds the segie steron on which moral judgment 18 Kant's theory is almost wholy concerned we 19 is defined as appealing to purient interests, with no social, scientific, or artistic mert in the United States, the courts have decided to take the meaning of obscenity to t material, as established by 21 The in the information and communication technology has in chances for misuse and criminal acts 22 There are diverse motivations for the socied programs theft, resentment and dissatisfaction, preventing software piracy, the challenge of per system's security, sabotage, philosophical belief in the right to free information, tun, personal satisfaction, etc 23 An important security-related aspect is data protection to maintain 24 is the quality or state of having no epistemic interactio from interference or intrusion through collecting private facts. 25 is the science of morais, the branch of knowledge that deals wil principles of human duty, or the logic of moral discourse, the whole field of morals c D climate of suspicion matura obligations 0 digitaromation dertienda atthies local community standards