Answered step by step
Verified Expert Solution
Question
1 Approved Answer
COMPUTER SECURITY So it basically says that if we use Facebook (as an example for our system), what are the good and bad implementaion example
COMPUTER SECURITY
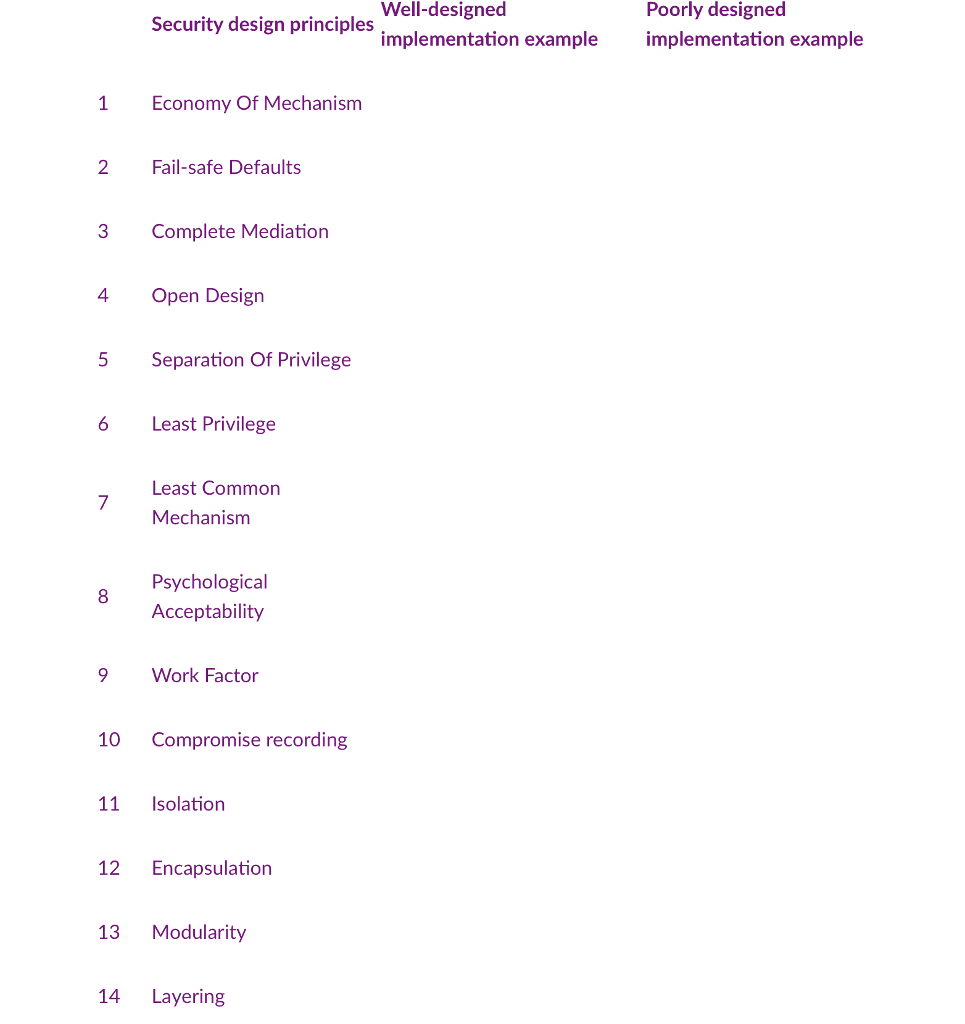
So it basically says that if we use Facebook (as an example for our system), what are the good and bad implementaion example be with regard to the 14 security principles.
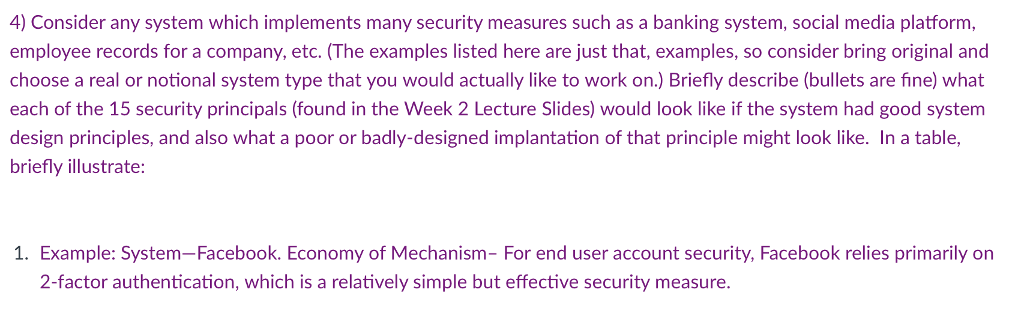
4) Consider any system which implements many security measures such as a banking system, social media platform, employee records for a company, etc. (The examples listed here are just that, examples, so consider bring original and choose a real or notional system type that you would actually like to work on.) Briefly describe (bullets are fine) what each of the 15 security principals (found in the Week 2 Lecture Slides) would look like if the system had good system design principles, and also what a poor or badly-designed implantation of that principle might look like. In a table, briefly illustrate: 1. Example: System-Facebook. Economy of Mechanism- For end user account security, Facebook relies primarily on 2-factor authentication, which is a relatively simple but effective security measureStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


