Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Concerning network security in the application layer. THANK YOU :) 2. Suppose Alice and Bob are sending packets to each other over a computer network.
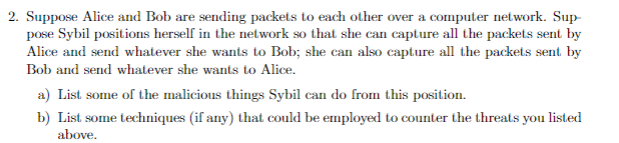
Concerning network security in the application layer. THANK YOU :) 2. Suppose Alice and Bob are sending packets to each other over a computer network. Sup pose Sybil positions herself in the network so that she can capture all the packets sent by Alice and send whatever she wants to Bob; she can also capture all the packets sent by Bob and send whatever she wants to Alice. a) List some of the malicious things Sybil can do from this position. b) List some techniques (if any) that could be employed to counter the threats you listed above
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


