Question
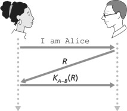
Consider Our authentication protocol as shown in Figure 1 in which Alice authenticates herself to Bob, which we saw works well (i.e., we found no
Consider Our authentication protocol as shown in Figure 1 in which Alice authenticates herself to Bob, which we saw works well (i.e., we found no flaws in it). Now suppose that while Alice is authenticating herself to Bob, Bob must authenticate himself to Alice. Give a scenario by which Trudy, pretending to be Alice, can now authenticate herself to Bob as Alice. (Hint: Consider that the sequence ofoperations Of the protocol, one with Trudy initiating and one with Bob initiating, can be arbitrarily interleaved. Pay particular attention to the fact that both Bob and Alice will use a nonce, and that if care is not taken, the same nonce can be used maliciously.) (Refer Figure I on google classroom)
Consider the 6-node network shown in figure 2, with the given link costs
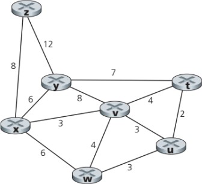
Using Dijkstra's algorithm, find the least cost path from source node x to all other destinations and
Show how the algorithm works by computing a table.(Refer figure 2 on google classroom) Solution
I am Alice R 12 8 7 y wStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started