Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Consider the following public key encryption scheme. The public key is (G, q, g, h) and the private key is x, generated exactly as in
Consider the following public key encryption scheme. The public key is (G, q, g, h) and the private key is x, generated exactly as in the El Gamal encryption shceme.
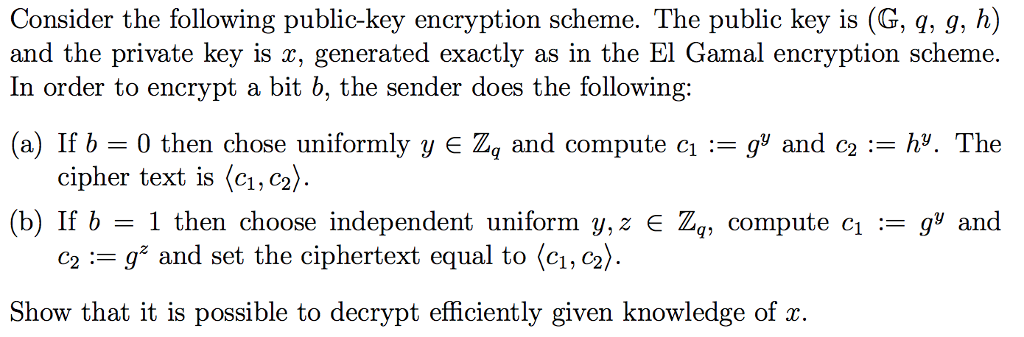
Consider the following public-key encryption scheme. The public key is (G, q, g, h) and the private key is x, generated exactly as in the El Gamal encryption scheme In order to encrypt a bit b, the sender does the following: (a) If b-0 then chose uniformly y E Zq and compute cg' and c- h. The cipher text is C1, C2) (b) If b = 1 then choose independent uniform y, z E Zq, compute ci-gy and c2-g" and set the ciphertext equal to C1, C2 Show that it is possible to decrypt efficiently given knowledge of x
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started