Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Consider the simple network shown below for a small company, with few resources to dedicate to network security. An intruder has access to the network
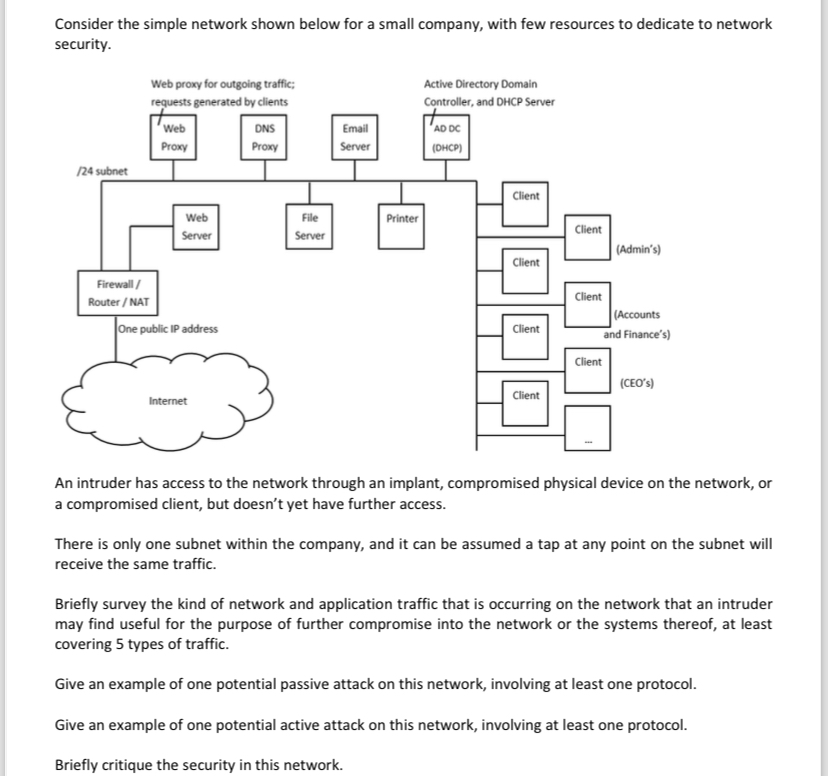
Consider the simple network shown below for a small company, with few resources to dedicate to network
security.
An intruder has access to the network through an implant, compromised physical device on the network, or
a compromised client, but doesn't yet have further access.
There is only one subnet within the company, and it can be assumed a tap at any point on the subnet will
receive the same traffic.
Briefly survey the kind of network and application traffic that is occurring on the network that an intruder
may find useful for the purpose of further compromise into the network or the systems thereof, at least
covering types of traffic.
Give an example of one potential passive attack on this network, involving at least one protocol.
Give an example of one potential active attack on this network, involving at least one protocol.
Briefly critique the security in this network.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


