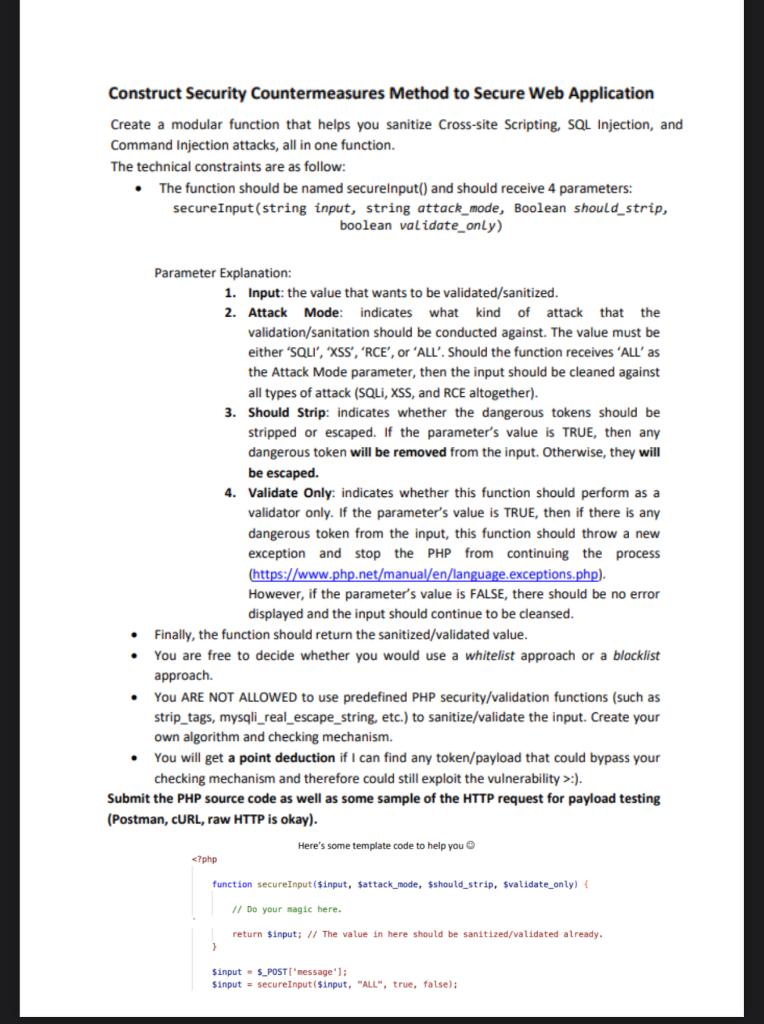
Construct Security Countermeasures Method to Secure Web Application Create a modular function that helps you sanitize Cross-site Scripting, SQL Injection, and Command Injection attacks, all in one function. The technical constraints are as follow: - The function should be named secureinput() and should receive 4 parameters: secureInput(string input, string attack_mode, Boolean should_strip, boolean validate_only) Parameter Explanation: 1. Input: the value that wants to be validated/sanitized. 2. Attack Mode: indicates what kind of attack that the validation/sanitation should be conducted against. The value must be either 'SQLI', 'XSS', 'RCE', or 'ALL'. Should the function receives 'ALL' as the Attack Mode parameter, then the input should be cleaned against all types of attack (SQLi, XSS, and RCE altogether). 3. Should Strip: indicates whether the dangerous tokens should be stripped or escaped. If the parameter's value is TRUE, then any dangerous token will be removed from the input. Otherwise, they will be escaped. 4. Validate Only: indicates whether this function should perform as a validator only. If the parameter's value is TRUE, then if there is any dangerous token from the input, this function should throw a new exception and stop the PHP from continuing the process (https://www.php.net/manual/en/language.exceptions.php). However, if the parameter's value is FALSE, there should be no error displayed and the input should continue to be cleansed. - Finally, the function should return the sanitized/validated value. - You are free to decide whether you would use a whitelist approach or a blocklist approach. - You ARE NOT ALLOWED to use predefined PHP security/validation functions (such as strip_tags, mysqli_real_escape_string, etc.) to sanitize/validate the input. Create your own algorithm and checking mechanism. - You will get a point deduction if I can find any token/payload that could bypass your checking mechanism and therefore could still exploit the vulnerability >: ). Submit the PHP source code as well as some sample of the HTTP request for payload testing (Postman, cURL, raw HTTP is okay). Here's some template code to help you