Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Create a Mathematica notebook that solves and discusses the solution. Create a general encryption and decryption functions for the hill cipher. Please using Mathematica! Thank
Create a Mathematica notebook that solves and discusses the solution. Create a general encryption and decryption functions for the hill cipher. 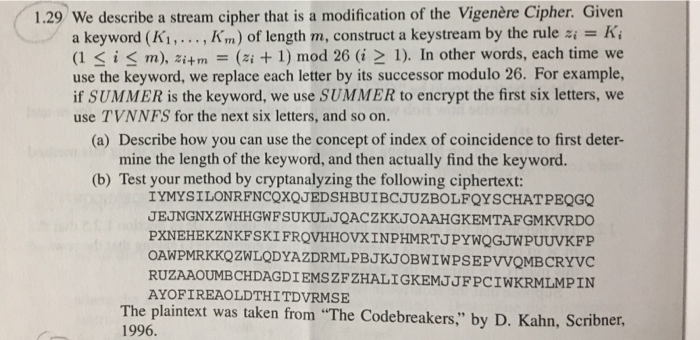
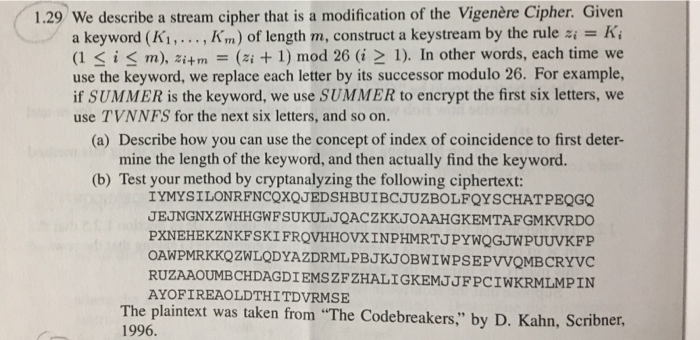
1.29 We describe a stream cipher that is a modification of the Vigenre Cipher. Given a keyword (K. . . . , Krn) of length m, construct a keystream by the rule si = Ki (I 1). In other words, each time we use the keyword, we replace each letter by its successor modulo 26. For example, if SUMMER is the keyword, we use SUMMER to encrypt the first six letters, we use TVNNFS for the next six letters, and so on. (a) Describe how you can use the concept of index of coincidence to first deter- mine the length of the keyword, and then actually find the keyword. (b) Test your method by cryptanalyzing the following ciphertext: IYMYSILONRFNCOXQJEDSHBUIBCJUZBOLFOYSCHATPEQGQ JEJNGNXZWHHGWFSUKULJQACZKKJOAAHGKEMTAFGMKVRDO PXNEHEKZNKFSKI FRQVHHOVXINPHMRTJPYWQGJWPUUVKFP OAWPMRKKQZWLQDYAZDRMLPBJKJOBWIWPSEPVVOMBCRYVC RUZAAOUMBCHDAGDIEMSZFZHALIGKEMJJFPCIWKRMLMPIN AYOFIREAOLDTHTDVRMSE The plaintext was taken from The Codebreakers," by D. Kahn, Scribner, 1996 Please using Mathematica! Thank you!
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started