Answered step by step
Verified Expert Solution
Question
1 Approved Answer
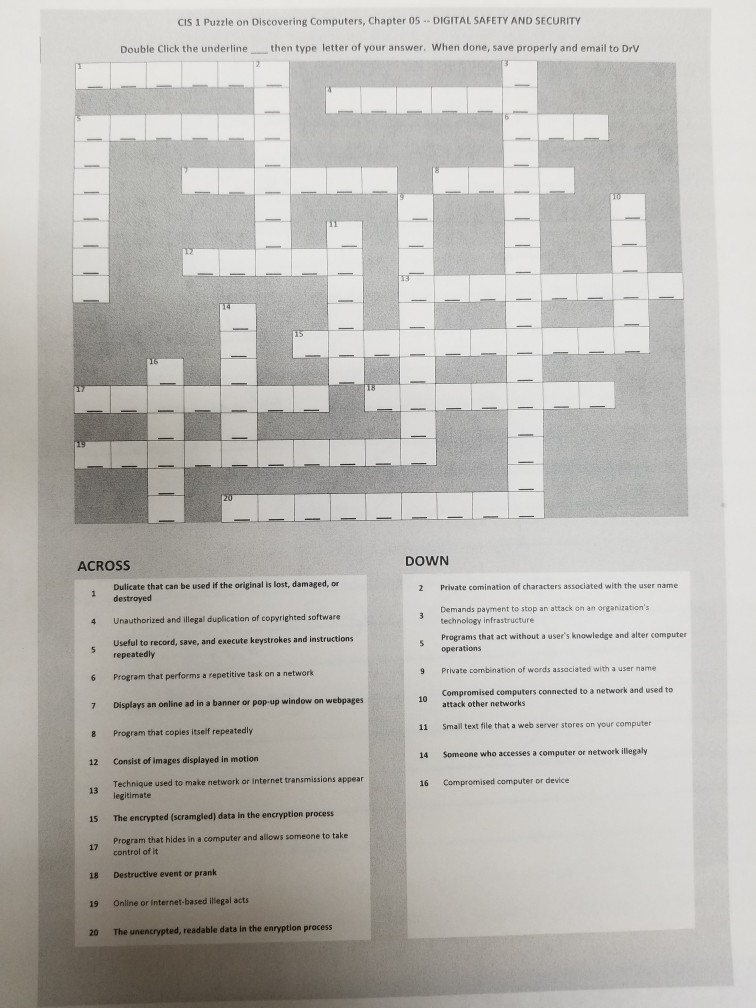
csi CIS 1 Puzzle on Discovering Computers, Chapter 05 DIGITAL SAFETY AND SECURITY Double Click the underlinethen type letter of your answer. When done, save
csi
CIS 1 Puzzle on Discovering Computers, Chapter 05 DIGITAL SAFETY AND SECURITY Double Click the underlinethen type letter of your answer. When done, save properly and email to Drv ACROSS DOWN Dulicate that can be used if the original is lost, damaged, or 2 Private comination of characters associated with the user name 1 destroyed Demands payment to stop an attack on an organization's technology infrastructure Programs that act without a user's knowledge and alter computer operations 4 Unauthorized and illegal duplication of copyrighted software Useful to record, save, and execute keystrokes and instructions repeatedly Private combination of words associated with a user name 6 Program that performs a repetitive task on a network 7 Displays an online ad in a banner or pop-up window on webpages 8 Program that copies itself repeatedly 12 Consist of images displayed in motion 13 legitimate 15 17 Program that hides in a computer and alows someone to take 9 Compromised computers connected to a network and used to attack other networks 10 Small text file that a web server stores on your computer Someone who accesses a computer or network illegaly Compromised computer or device 11 14 Technique used to make network or internet transmissions appear 16 The encrypted (scramgled) data in the encryption process control of it Destructive event or prank Online or internet-based illegal acts The unencrypted, readable data in the enryption process 18 19 20Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


