Answered step by step
Verified Expert Solution
Question
1 Approved Answer
CyberLab Assignment # 3 EndsJul 2 1 For this assignment, you are going to learn and give a step - by - step tutorial on
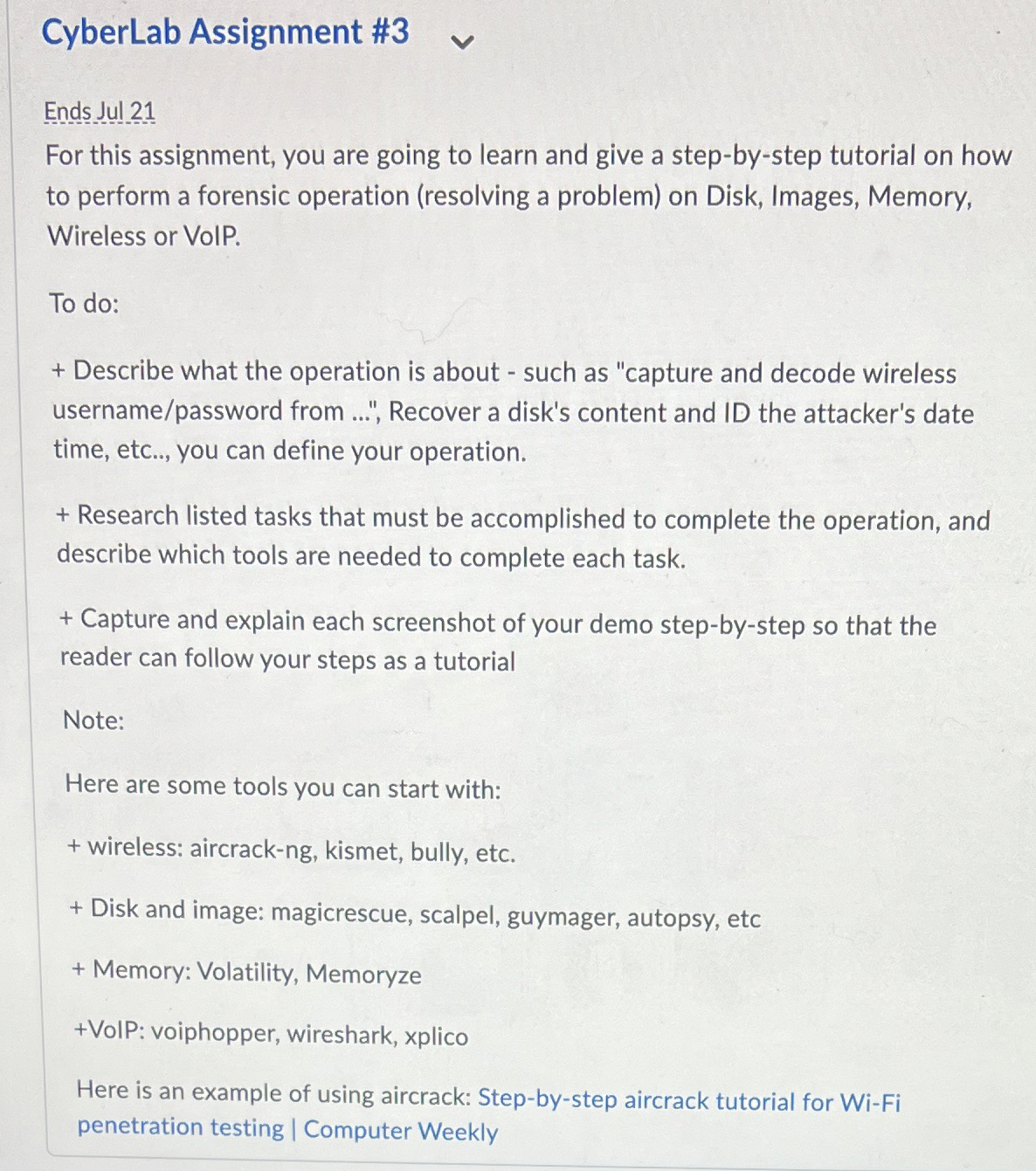
CyberLab Assignment #
EndsJul
For this assignment, you are going to learn and give a stepbystep tutorial on how to perform a forensic operation resolving a problem on Disk, Images, Memory, Wireless or VolP.
To do:
Describe what the operation is about such as "capture and decode wireless usernamepassword from Recover a disk's content and ID the attacker's date time, etc.., you can define your operation.
Research listed tasks that must be accomplished to complete the operation, and describe which tools are needed to complete each task.
Capture and explain each screenshot of your demo stepbystep so that the reader can follow your steps as a tutorial
Note:
Here are some tools you can start with:
wireless: aircrackng kismet, bully, etc.
Disk and image: magicrescue, scalpel, guymager, autopsy, etc
Memory: Volatility, Memoryze
VoIP: voiphopper, wireshark, xplico
Here is an example of using aircrack: Stepbystep aircrack tutorial for WiFi penetration testing Computer Weekly
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


