Answered step by step
Verified Expert Solution
Question
1 Approved Answer
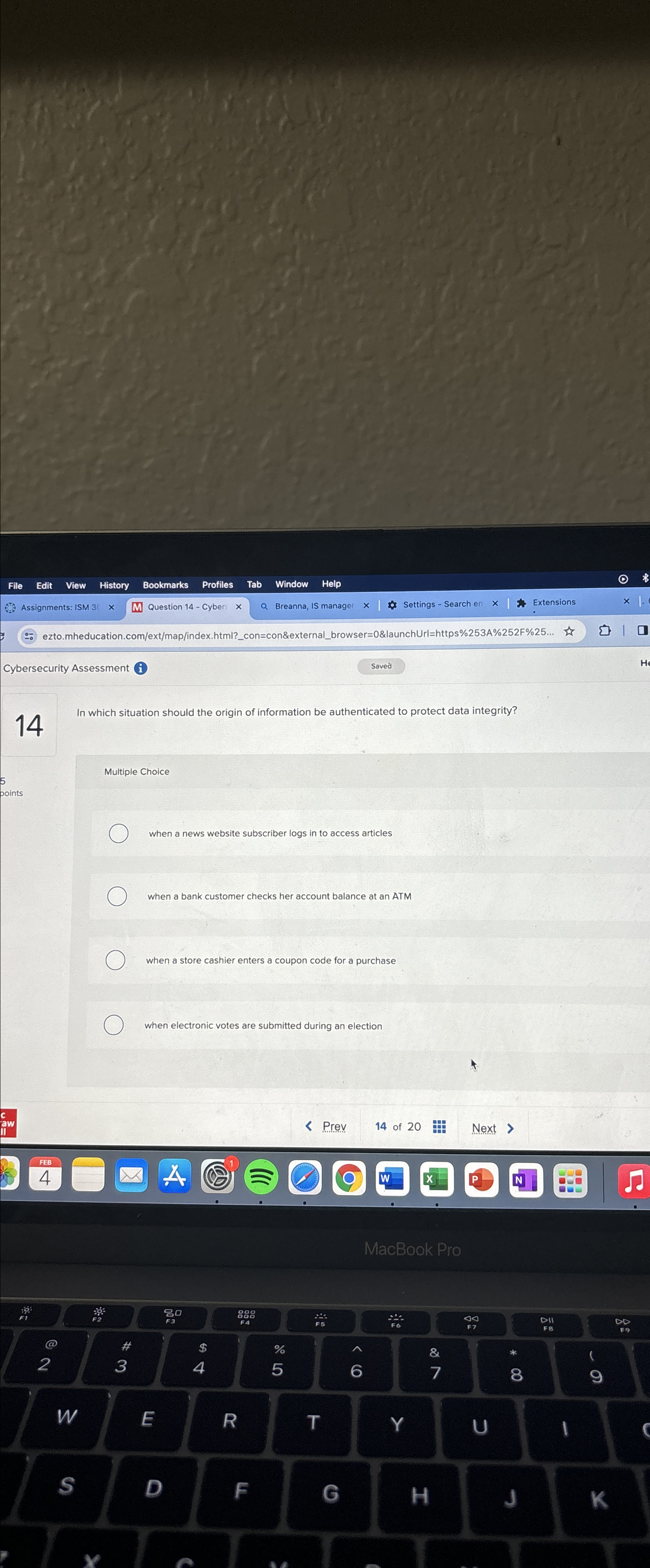
Cybersecurity Assessment ( i 1 4 In which situation should the origin of information be authenticated to protect data integrity? Multiple Choice when a news
Cybersecurity Assessment i
In which situation should the origin of information be authenticated to protect data integrity?
Multiple Choice
when a news website subscriber logs in to access articles
when a bank customer checks her account balance at an ATM
when a store cashier enters a coupon code for a purchase
when electronic votes are submitted during an election
Prev
of
Next
D
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


