Answered step by step
Verified Expert Solution
Question
1 Approved Answer
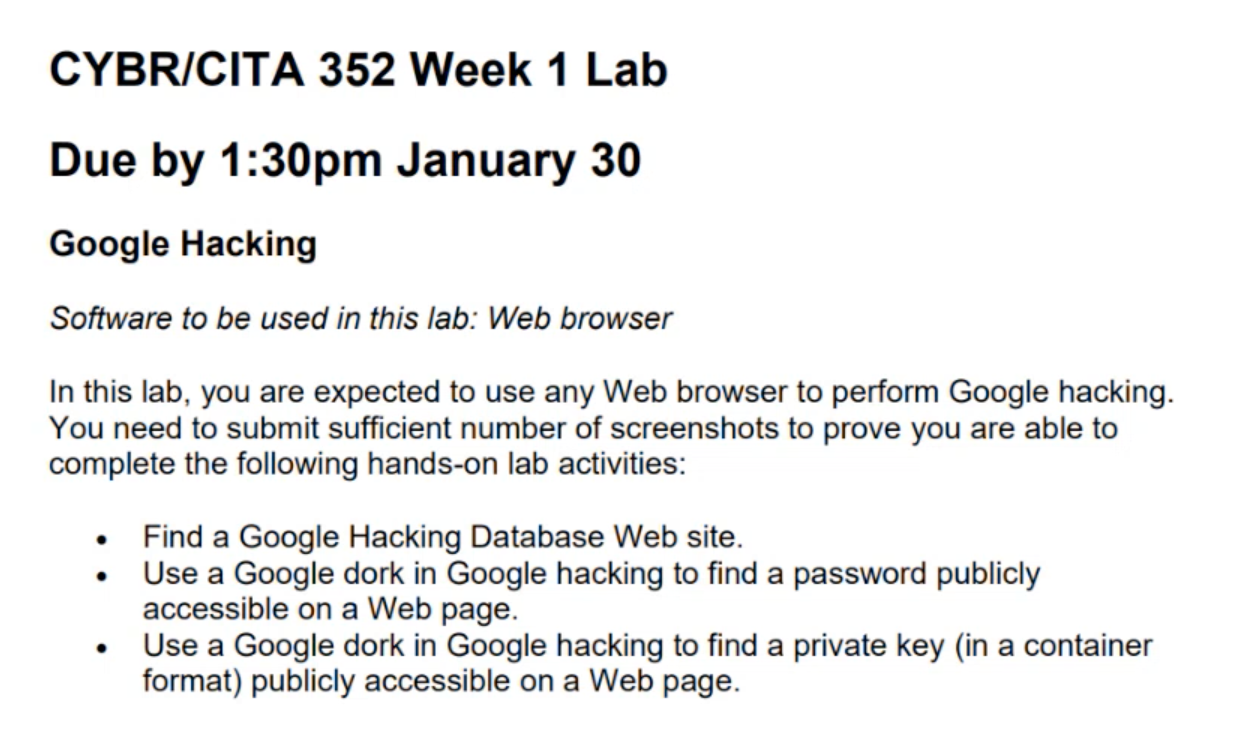
CYBR / CITA 3 5 2 Week 1 Lab Due by 1 : 3 0 pm January 3 0 Google Hacking Software to be used
CYBRCITA Week Lab
Due by :pm January
Google Hacking
Software to be used in this lab: Web browser
In this lab, you are expected to use any Web browser to perform Google hacking.
You need to submit sufficient number of screenshots to prove you are able to
complete the following handson lab activities:
Find a Google Hacking Database Web site.
Use a Google dork in Google hacking to find a password publicly
accessible on a Web page.
Use a Google dork in Google hacking to find a private key in a container
format publicly accessible on a Web page.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


