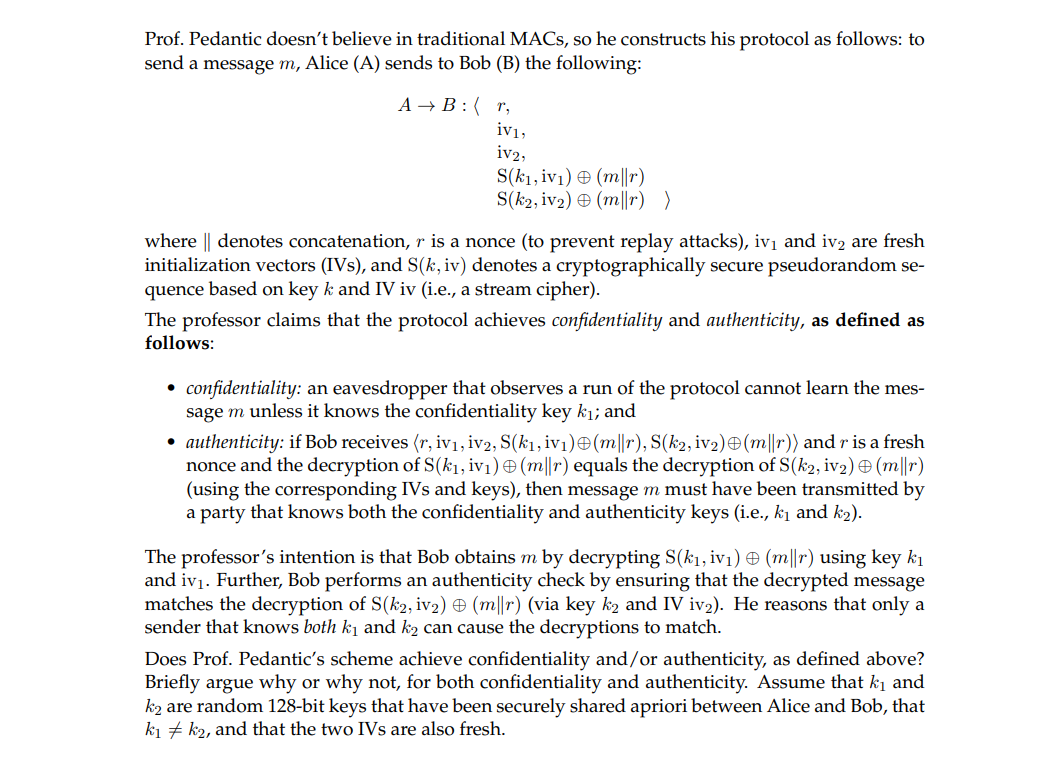
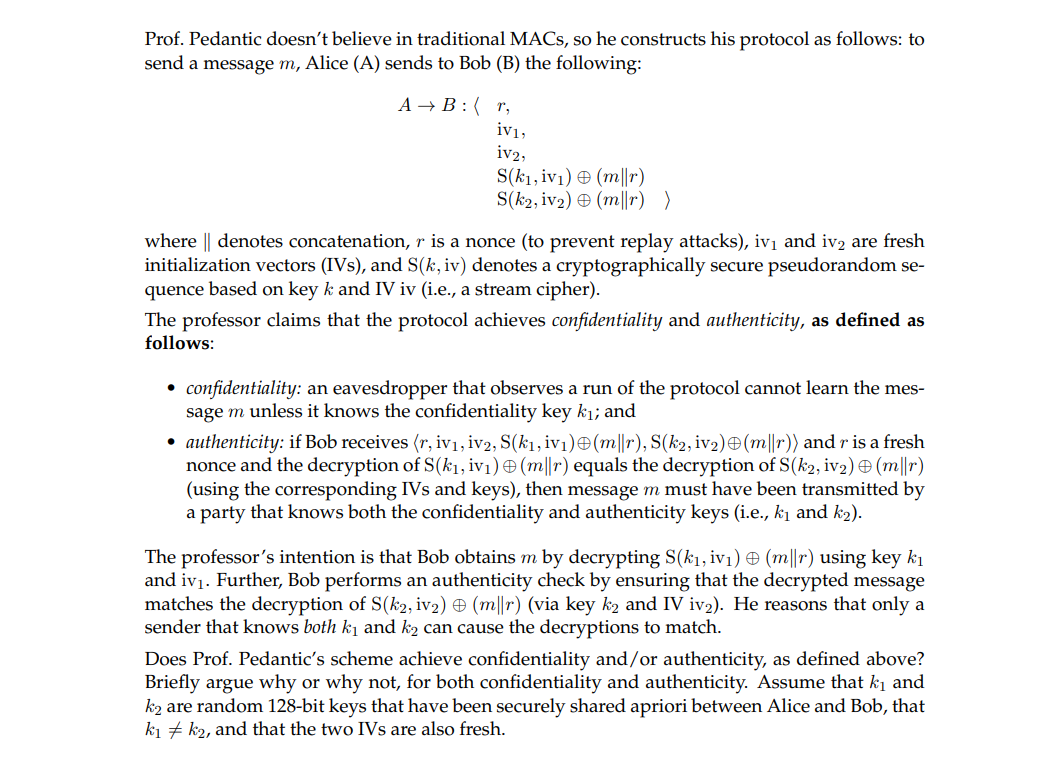
(d) {15 points } Prof. Pedantic designed a "secure" communication protocol for two parties (Alice and Bob) that have preshared secrets k1 (the confidentiality key) and k2 (the authenticity key). "Last revised on February 4, 2023. 1 Extra credit {0.0000001 points } : Explain that joke. 1 Prof. Pedantic doesn't believe in traditional MACs, so he constructs his protocol as follows: to send a message m, Alice (A) sends to Bob (B) the following: Prof. Pedantic doesn't believe in traditional MACs, so he constructs his protocol as follows: to send a message m, Alice (A) sends to Bob (B) the following: AB:r,iv1,iv2,S(k1,iv1)(mr)S(k2,iv2)(mr) where denotes concatenation, r is a nonce (to prevent replay attacks), iv 1 and iv2 are fresh initialization vectors (IVs), and S(k, iv) denotes a cryptographically secure pseudorandom sequence based on key k and IV iv (i.e., a stream cipher). The professor claims that the protocol achieves confidentiality and authenticity, as defined as follows: - confidentiality: an eavesdropper that observes a run of the protocol cannot learn the message m unless it knows the confidentiality key k1; and - authenticity: if Bob receives r,iv1,iv2,S(k1,iv1)(mr),S(k2,iv2)(mr) and r is a fresh nonce and the decryption of S(k1,iv1)(mr) equals the decryption of S(k2,iv2)(mr) (using the corresponding IVs and keys), then message m must have been transmitted by a party that knows both the confidentiality and authenticity keys (i.e., k1 and k2 ). The professor's intention is that Bob obtains m by decrypting S(k1, iv 1)(mr) using key k1 and iv1. Further, Bob performs an authenticity check by ensuring that the decrypted message matches the decryption of S(k2,iv2)(mr) (via key k2 and IViv2 ). He reasons that only a sender that knows both k1 and k2 can cause the decryptions to match. Does Prof. Pedantic's scheme achieve confidentiality and/or authenticity, as defined above? Briefly argue why or why not, for both confidentiality and authenticity. Assume that k1 and k2 are random 128-bit keys that have been securely shared apriori between Alice and Bob, that k1=k2, and that the two IVs are also fresh