Answered step by step
Verified Expert Solution
Question
1 Approved Answer
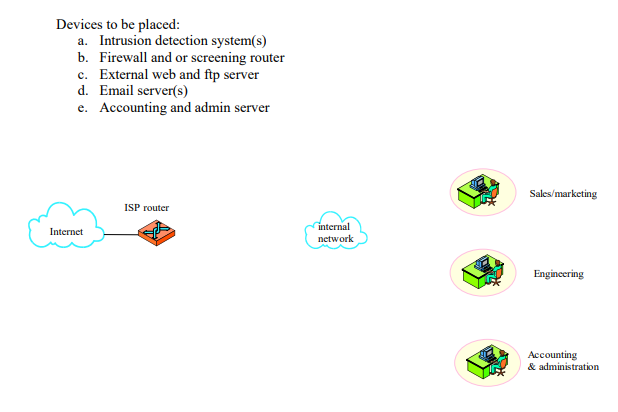
Develop a plan to deploy the following devices. Include the following information for each device. (30 points) a. Show where you would deploy the device
Develop a plan to deploy the following devices. Include the following information for each device. (30 points) a. Show where you would deploy the device using the diagram b. Any device characteristics (type, etc.) c. Any weaknesses or vulnerabilities The goals for the deployment are: 3 Access to the Internet by the internal users External web, ftp server Protection from internal and external attacks Email service for all Internal protection of the administrative servers
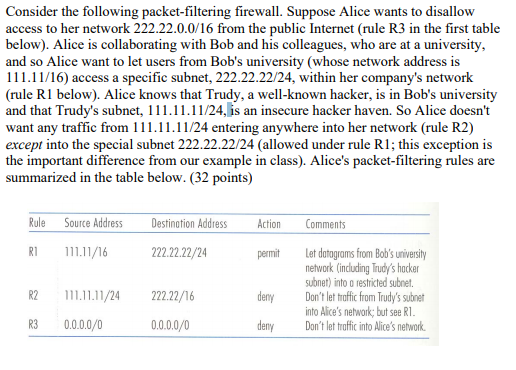
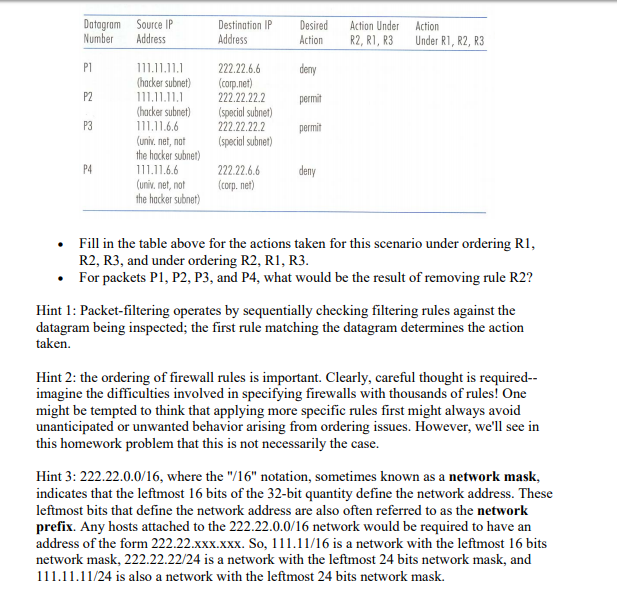
Consider the following packet-filtering firewall. Suppose Alice wants to disallow access to her network 222.22.0.0/16 from the public Internet (rule R3 in the first table below). Alice is collaborating with Bob and his colleagues, who are at a university, and so Alice want to let users from Bob's university (whose network address is 111.11/16) access a specific subnet, 222.22.22/24, within her company's network (rule R1 below). Alice knows that Trudy, a well-known hacker, is in Bob's university and that Trudy's subnet, 111.11.11/24, is an insecure hacker haven. So Alice doesn't want any traffic from 11.11.11/24 entering anywhere into her network (rule R2) except into the special subnet 222.22.22/24 (allowed under rule R1; this exception is the important difference from our example in class). Alice's packet-filtering rules are summarized in the table below. (32 points) Rule Soure Adress Destination Adress Action Comments R 1/16 222.22.22/24 Let datagrams from Bob's university nehwork (inluding Trudy's hacke subnet) into o restricted subnet. Don't let thraffic from Trudy's subne into Alice's network, but see R permit R2 1111/24 222.22/16 deny R3 0.0.0.0/0 0.0.0.0/0 denry Don't let traffic into Alice's network Consider the following packet-filtering firewall. Suppose Alice wants to disallow access to her network 222.22.0.0/16 from the public Internet (rule R3 in the first table below). Alice is collaborating with Bob and his colleagues, who are at a university, and so Alice want to let users from Bob's university (whose network address is 111.11/16) access a specific subnet, 222.22.22/24, within her company's network (rule R1 below). Alice knows that Trudy, a well-known hacker, is in Bob's university and that Trudy's subnet, 111.11.11/24, is an insecure hacker haven. So Alice doesn't want any traffic from 11.11.11/24 entering anywhere into her network (rule R2) except into the special subnet 222.22.22/24 (allowed under rule R1; this exception is the important difference from our example in class). Alice's packet-filtering rules are summarized in the table below. (32 points) Rule Soure Adress Destination Adress Action Comments R 1/16 222.22.22/24 Let datagrams from Bob's university nehwork (inluding Trudy's hacke subnet) into o restricted subnet. Don't let thraffic from Trudy's subne into Alice's network, but see R permit R2 1111/24 222.22/16 deny R3 0.0.0.0/0 0.0.0.0/0 denry Don't let traffic into Alice's network
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started