Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Directions A business you are working with has a public key that they are hoping to distribute to clients. Their clients want to download the
Directions
A business you are working with has a public key that they are hoping to distribute to clients. Their clients want to download the public key
from a website and verify the key with a checksum. To accomplish this, you will need to code a simple string checksum verification program. In
addition, you will need to document your process by completing the Module Five Coding Assignment Checksum Verification Template, linked
in What to Submit.
Specifically, you must address the following rubric criteria:
Algorithm Cipher: Recommend an appropriate encryption algorithm cipher that avoids collisions.
a To do so review the scenario and the Java Security Standard Algorithm Names, which is a standard list of algorithm ciphers provided by
Oracle.
b Document your recommendation in the template provided.
Justification: Justify your reasoning for the recommended algorithm cipher that avoids collisions.
a To do so provide a brief, highlevel overview of the encryption algorithm software. Consider what it means to avoid collisions. Why is
this important?
b Document your reasoning in the template provided.
Generate Checksum: Refactor the code to encrypt a text string and generate a checksum verification.
a To do so first download the Module Five Coding Assignment Checksum Verification Code Base, linked in the Supporting Materials
section, and upload it to Eclipse as a new project. Refactor the code to add your first and last name as a unique data string. You will
submit your refactored code for your instructor to review. Then generate the checksum by following these steps:
i Create an object of MessageDigest class using the java.security.MessageDigest library.
ii Initialize the object with your selection for an appropriate algorithm cipher.
iii. Use the digest method of the class to generate a hash value of byte type from the unique data string your first and last name
iv Convert the hash value to hex using the bytesToHex function.
v Create a RESTFul route using the @RequestMapping method to generate and return the required information to the web browser,
including the hash value.
Verification: Demonstrate that a hash value has been created for the unique text string your first and last name by executing the Java
code.
a Then use your web browser to connect to the RESTful API server. It should show your first and last name as the unique data string in
the browser, the name of the algorithm cipher you used, and the checksum hash value.
b Capture a screenshot of the web browser with your unique information and add it to the template provided. An example of the
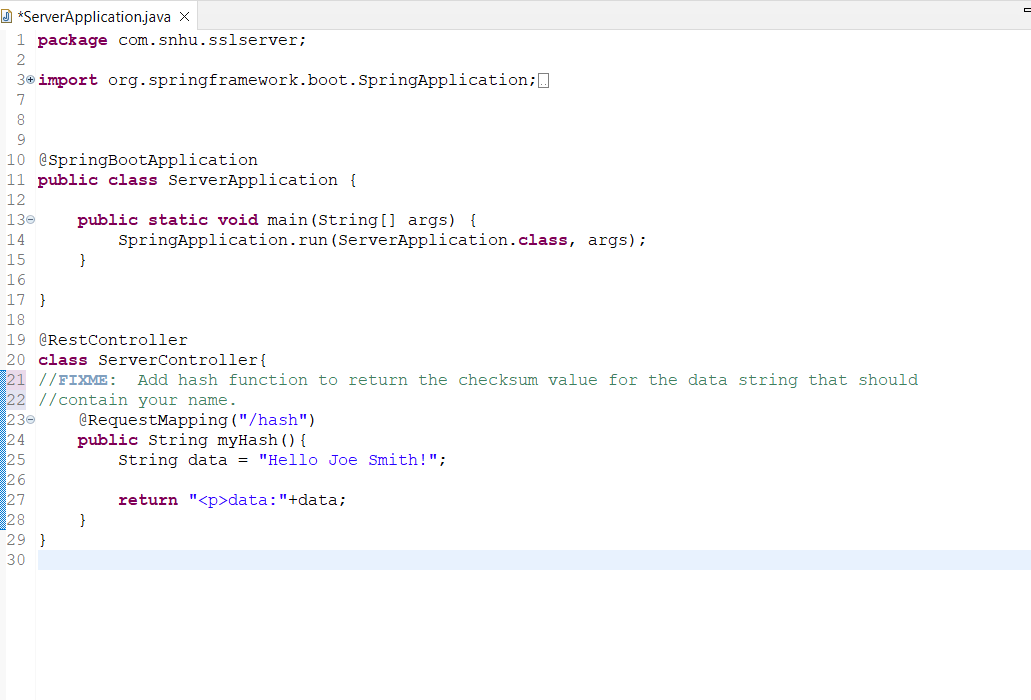
expected output is shown below:package com.snhu.sslserver;
GIVEN CODE:
import org.springframework.boot.SpringApplication;
aSpringBootApplication
public class ServerApplication
public static void mainString args
SpringApplication. run ServerApplicationclass, args;
@RestController
class ServerController
FIXVE: Add hash function to return the checksum value for the data string that should
contain your name.
@RequestMapping hash
public String myHash
String data "Hello Joe Smith!";
return "data:"data;
Given POM.xml:
org.springframework.boot
springbootstarterparent
RELEASE
com.snhu
sslserver
SNAPSHOT
sslserver
sslserver skeleton for CS
org.springframework.boot
springbootstarterdatarest
org.springframework.boot
springbootstarterweb
org.springframework.boot
springbootstartertest
test
org.junit.vintage
junitvintageengine
org.springframework.boot
springbootmavenplugin
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


