Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Discuss the following: When using a public cryptographic hash function, how to add a shared key into message to compute a hash value so that
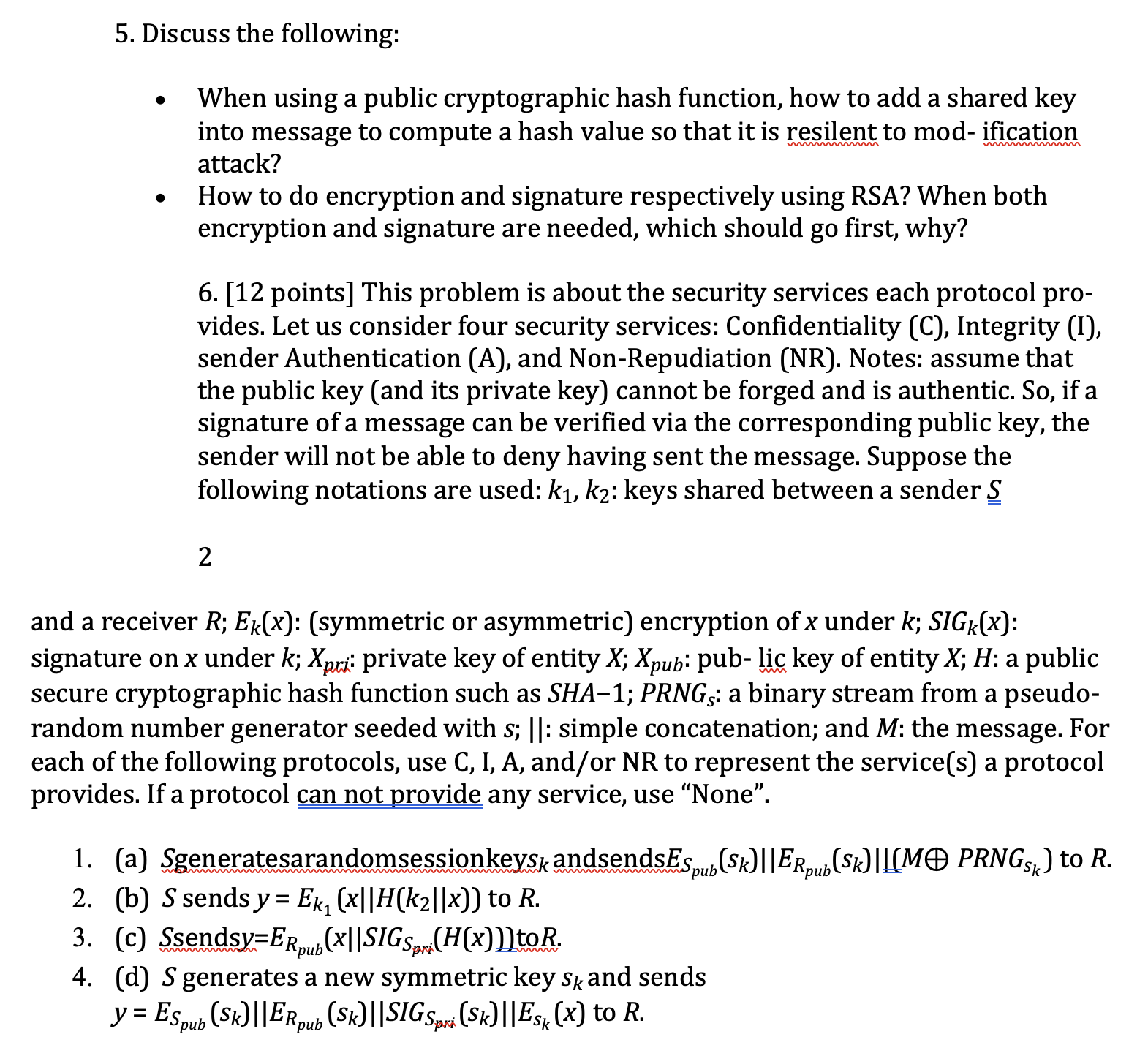
Discuss the following:
When using a public cryptographic hash function, how to add a shared key
into message to compute a hash value so that it is resilent to mod ification
attack?
How to do encryption and signature respectively using RSA? When both
encryption and signature are needed, which should go first, why?
points This problem is about the security services each protocol pro
vides. Let us consider four security services: Confidentiality C Integrity I
sender Authentication A and NonRepudiation NR Notes: assume that
the public key and its private key cannot be forged and is authentic. So if a
signature of a message can be verified via the corresponding public key, the
sender will not be able to deny having sent the message. Suppose the
following notations are used: : keys shared between a sender
and a receiver ; : symmetric or asymmetric encryption of under ; :
signature on under ; : private key of entity ; : pub lic key of entity ; : a public
secure cryptographic hash function such as SHA; : a binary stream from a pseudo
random number generator seeded with ; II: simple concatenation; and : the message. For
each of the following protocols, use C I, A andor NR to represent the services a protocol
provides. If a protocol can not provide any service, use "None".
a Sgeneratesarandomsessionkeys andsends to
b sends to
c sendsy to
d generates a new symmetric key and sends
to
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started