Answered step by step
Verified Expert Solution
Question
1 Approved Answer
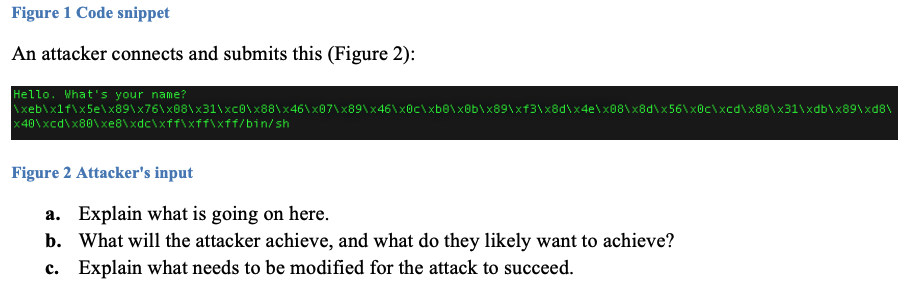
Figure 1 Code snippet An attacker connects and submits this (Figure 2): Hello. What's your name? xebx1fx5ex80x76x68x31xCOx88x46x67x89x46x0cxbexxObx89x63x8dx4ex68x8dx56x0cxcdx80x31xdbx89xd8 *40xcdx80xe8xdcixffixffixff/bin/sh Figure 2 Attacker's input a. Explain what
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started